In this article, we discuss ways to bypass VPN blocks. Using a VPN is a great way to beat internet censorship. Under normal circumstances, all you need do is connect to a VPN server located somewhere that is not censored, and you have uncensored access to the internet.
The problem, of course, is that this feature of VPNs is well-known. And as a result, those who would censor your internet also try to block the use of VPNs to bypass their censorship...
Internet censorship
Internet censorship comes in many shapes and sizes. Common examples include:
Government censorship for political and/or social reasons
Classic examples include the Great Firewall of China and state censorship in Iran. The UAE has also recently hit the headlines for criminalizing the use of VPNs and the like to bypass its censorship restrictions. For more information about using a VPN to bypass censorship in these countries see our VPN for UAE and VPN for China guides.
Government censorship for copyright reasons
It is becoming increasingly common for governments to block access to websites that are deemed to promote or facilitate copyright piracy. This form of censorship is particularly common in European counties, with the UK leading the charge. Russia has also recently ramped-up its efforts to block access to pirated content.
Work
Many workplaces try to prevent employees from accessing content that might upset or offend other colleagues (see Not safe for work). Or which is likely to distract them from work (such as chatting on social media). Such restrictions are usually quite understandable in the context of a working environment.
Schools and colleges
It is common for educational institutions to block access to web content. When the pupils are minors, this is arguably justified. It is less so, though, at universities and higher education establishments where the attendees are adults. Indeed, the notion of censorship at higher educational institutions is more than a little ironic!
Porn, social media, and websites linked to copyright infringement are usually the main targets. It is not uncommon, however, for political content to be censored.

Even more worrying is denying young people access to important information relating to social issues such as drug advice, sexual health, racial and/or sexual discrimination, bullying, and more.
Websites that block VPNs
It is becoming increasingly common for media streaming websites to block viewers who use VPNs bypass geo-restrictions placed on their services. Prime examples include Hulu, US Netflix, and BBC iPlayer.
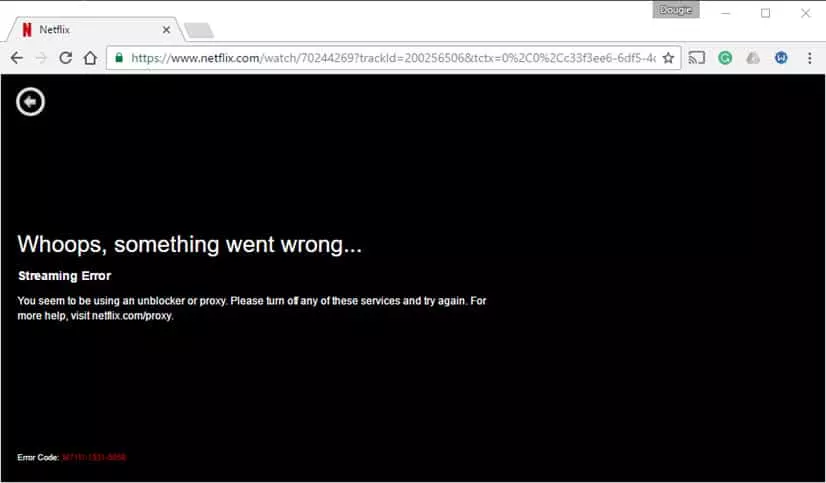
The reason for such blocks is almost always because copyright holders want to maximize their profits by artificially segregating the world market.
Legal considerations
VPN blocks are put into place for a reason, and the people placing them usually take a dim view of efforts to evade their blocks.
That said, even in countries where VPNs are blocked (such as China and Iran), their use is almost never actually illegal. This means that evading VPN blocks will almost never get you into trouble with the law.
A notable exception to this general rule is the UAE, which has recently announced that anyone caught using a VPN risk a fine of up to 2 Million UAE Dirham (over US$500,000) and/or prison time. How rigorously this is enforced in practice remains to be seen, but caution is strongly advised when trying to evade VPN blocks in the UAE.
Of course, even though using a VPN and bypassing VPN restrictions are not usually illegal, per se, the content you access when using the VPN may be.
Safety considerations
When using a private WiFi or LAN network, the owner of that network has every legal right to restrict what you can do when connected to their network. This includes school, university, office, and home networks, etc.
The chances of getting caught evading VPN restrictions on such networks is usually quite slim, but can potentially result in suspension, sacking, and other disciplinary measures.
It is, therefore, worth carefully considering whether the benefit of evading VPN blocks justifies the potential problems, should you get caught.
How VPN blocks work
VPN use can be prevented in a number of ways, and organizations that are serious about blocking VPNs often combine techniques.
Note that with the exception of China (where all internet traffic to and from China is restricted to just 3 government controlled access points), government VPN blocks (and censorship) is almost always actually performed by ISPs at the government’s instruction.
Common tactics for VPN blocks include:
Blocking access to VPN websites
If you can’t access a VPN provider’s website then you can’t sign-up for its service or download its software. This form of censorship usually extends to VPN review websites (such as ProPrivacy.com) and other websites dedicated to methods of evading censorship.
Although rarely the only tactic employed, blocking access to VPN websites is a very common addition to other methods used.
Blocking IPs of known VPN servers
It is not too difficult to discover the IP addresses of the VPN servers used by VPN providers. And then block access to them.
This is by far the most common method of preventing VPN use, and when used together with blocking access to VPN websites, is usually the extent of most VPN blocks.
Given the large number of VPN providers out there, and the difficulty of keeping track of changing server IP addresses, most organizations settle for banning just the more popular VPN services. This means that users of smaller and less well-known VPN services can often "slip under the radar”.
Port blocking
By default, OpenVPN uses port 1194 (UDP, although this can be easily changed to TCP). Other VPN protocols use different ports. A simple but effective way to block VPNs, therefore, is to use a firewall to block these ports.
Deep packet inspection (DPI)
Deep packet inspection is "a form of computer network packet filtering that examines the data part (and possibly also the header) of a packet as it passes an inspection point.” Various technologies are used for DPI, with varying levels of effectiveness.
Data encapsulated by VPN protocols, however, is pretty easy to spot using even fairly basic DPI techniques. The content of the packets remains securely encrypted, but DPI can determine that it has been encrypted using a VPN protocol.
Using DPI to detect VPN traffic is definitely a step up in seriousness on the part of the organization performing the DPI.
Simple Solutions
Use a mobile connection
Ok, so this won’t work for evading government blocks, but it will work schools, colleges, at work, etc. And it is often by far the easiest solution. Rather than using a VPN to access content blocked on the local network, just access it on your mobile device using your mobile (cellular) connection.
This does mean that you will have to pay your usual mobile data charges, but it allows you to check your Facebook account without with little effort and little chance of getting into trouble for it.
Try a different VPN provider and/or servers
As already noted, keeping track of all IP addresses belonging to all VPN providers is a momentous task. Switching to a lower-profile VPN service is therefore often enough to evade blanket IP blocks. Even if some IPs belonging to a particular VPN blocked, simply changing to different ones run by the same provider might work.
Some VPN providers regularly recycle their IP addresses. This makes keeping track of the changes and blocking the new IPs a major headache. This tactic is often referred to as a game of "whack-a-mole”. It is worth asking your provider if this is something that it does.
Not many VPN providers currently fully support IPv6 (Mullvad is the only one I know of). This is almost certain to change, however, as new IPv4 addresses become unavailable. IPv6 hugely expands the number of IP addresses available. This means that as IPv6 becomes more widely adopted, simple IP blocks will become less and less effective.
Roll your own VPN
A more extreme but highly effective option is to run your own VPN server and then connect to it from the censored location.
As the VPN server belongs to you, this does not provide the usual privacy benefits of using a commercial VPN service. It does, however, provide you with your very own unique VPN IP address, which will not be blocked.
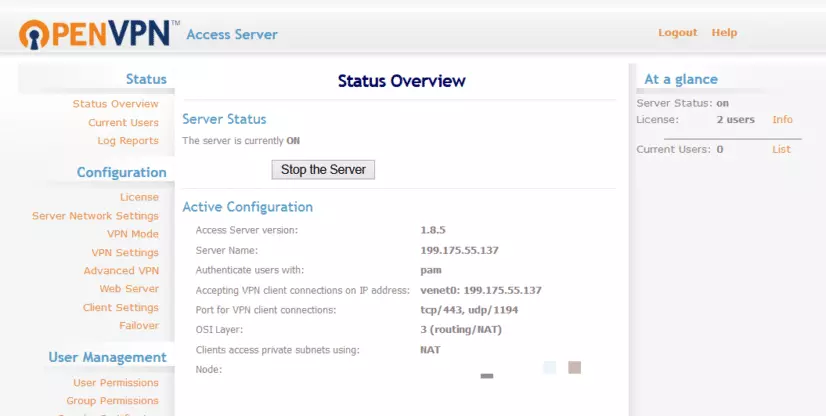
You can setup a home PC to act as your personal VPN server, or rent and configure a VPS (which is also great for geospoofing). If rolling your own VPN on a VPS seems too hard, PrivatePackets.io can do the heavy lifting for you.
Dedicated IP addresses
Some VPNs offer dedicated IP addresses. This means that instead of sharing an IP with many other users, you are assigned a unique IP (much like if you roll your own VPN ). Because this IP is unique to you, it is very unlikely to be blocked by websites such as Netflix and BBC iPlayer. As with rolling your own VPN, though, it does not have the privacy benefits of using a shared IP address. Check out our VPN for iPlayer page for more information about unblocking British content.
Come prepared
When visiting places such as China, one of the most effective tactics is simply come prepared! Signup for a VPN service and download its software before your visit. Even when access to access to VPN providers’ websites is blocked, VPN connections themselves are often not.
If you have failed to come prepared (or never had the opportunity), alternative censorship-busting technologies can be used to access VPN websites. You can then sign-up and download their software.
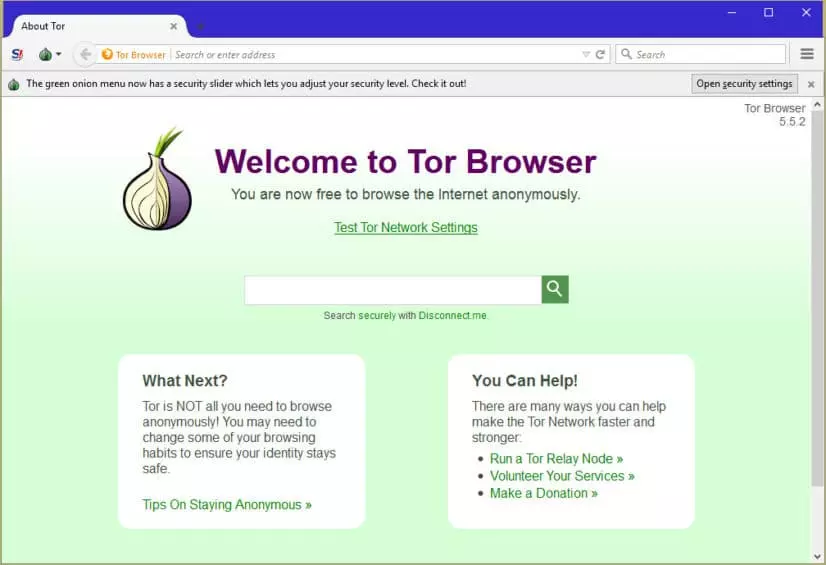
Tor network
Tor is better at providing anonymity than it is at censorship-busting. This is because of the ease with which access to Tor nodes can be blocked. Tor bridges can be used to bypass IP blocks on Tor nodes, and obfsproxy (see below) can be used to hide Tor traffic from Deep packet inspection.
Shadowsocks (Chinese: 影梭)
This "is an open-source proxy application, widely used in mainland China to circumvent Internet censorship.” It is an open source anti-GFW tool/protocol/server created by a Chinese developer. Basically it’s a SOCKS5 proxy that is available for most major platforms.
Surge
This is similar to Shadowsocks, but is only available for iOS.
Lahana
Derived from Tor, Lahana is designed to solve Tor’s problem with easily blocked exit nodes by making it "stupidly easy” to setup new nodes. Lahana was designed to defeat censorship in Turkey, but should also work well in many other censorship situations.
Psiphon
This uses a combination of VPN, SSH and obfuscation technologies to bypass censorship. If you encounter a block when using VPN, for example, you can switch to SSH or obfuscated SSH (SSH+) instead. One of the best things about Psiphon is that if you find the Psiphon website blocked, you can request the software be sent to you via email.
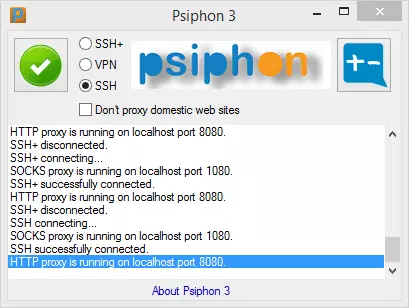
In fact, most VPN providers will also be happy let you sign up and download their software via email. Just ask.
Change port numbers
Many custom VPN clients allow you change the port they use. This is a good way to defeat port blocking. The two most popular choices of port to use are:
TCP port 80 - this is the port uses by all "normal” unencrypted internet traffic. In other words, it is the port used by HTTP. Blocking this port effectively blocks the internet, and is therefore almost never done. The downside is that even the most primitive DPI techniques will spot VPN traffic using this port.
TCP port 443 – this is the port used by HTTPS, the encrypted protocol that secures all secure websites. Without HTTPS no form of online commerce, such as shopping or banking, would be possible. It is therefore very rare for this port to be blocked.
And as an added bonus, VPN traffic on TCP port 443 is routed inside the TLS encryption used by HTTPS. This makes it much harder to spot using DPI. TCP port 443 is therefore the favored port for evading VPN blocks.
Many VPN providers offer the ability to change port numbers using their custom software (especially when using the OpenVPN protocol).
Even if yours does not, many VPN providers do actually support OpenVPN using TCP port 443 at the server level. You can switch to it with a simple edit to your OpenVPN configuration (.ovpn) file. It is therefore worth asking your VPN provider about this.
Another option is to use the SSTP protocol (if available), which uses TCP port 443 by default.
Advanced solutions
Some VPN providers offer more advanced VPN blocking solutions designed to defeat more sensitive DPI techniques. Such techniques analyze packet size and/or timing to detect OpenVPN’s rather distinctive handshake, even when hidden behind HTTPS.
Very sensitive (and therefore also very expensive, and rarely used) DPI may even detect VPN use when using the tactics outlined below. There are 2 basic approaches to advanced VPN concealment:
stunnel / SSL tunneling
stunnel is an open source multi-platform program that creates TLS/SSL tunnels. TLS/SSL is the encryption used by HTTPS, so VPN connections (usually OpenVPN) routed through these TLS/SSL tunnels are therefore very difficult to tell apart from regular HTTPS traffic.
This is because the OpenVPN data is wrapped inside an additional layer of TLS/SSL encryption. As DPI techniques are unable to penetrate this "outer” layer of encryption, they are unable to detect the OpenVPN encryption "inside”.
SSL tunnels are usually made using the stunnel software. This must be configured on both the VPN server and your computer. It is, therefore, necessary to discuss the situation with your VPN provider if you want to use SSL tunneling (a setup guides is available here for reference).
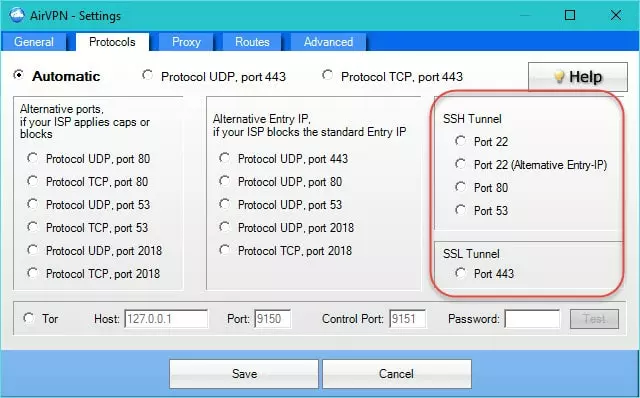
AirVPN is the only VPN provider I know of to offer stunnel functionality "out of the box” using its custom open source software. I am not otherwise familiar with Anonyproz, but it can be configured for stunnel, and other providers might also offer this feature.
SSH tunnelling
This is similar to SSL tunneling, except that the VPN data is wrapped inside a layer of Secure Shell (SSH) encryption instead. SSH is used primarily for accessing shell accounts on UNIX systems. Its use is mainly restricted to the business world, and is nowhere near as popular as SSL.
As with SSL tunneling, you will need to talk to your VPN provider to get it working.
Obfsproxy (and similar technologies)
Obfsproxy is a tool designed to wrap data into an obfuscation layer. This makes it difficult to detect that OpenVPN (or any other VPN protocol) is being used.
It has been adopted by the Tor network, largely as a response to China blocking access to public Tor nodes. It is independent of Tor, however, and can be configured for OpenVPN .
To work, obfsproxy needs to be installed on both the client’s computer (using, for example, port 1194), and the VPN server. However, all that is then required is that the following command line be entered on the server:
obfsproxy obfs2 –dest=127.0.0.1:1194 server x.x.x.x:5573
This tells obfsproxy to listen on port 1194 (for example), to connect locally to port 1194 and forward the de-encapsulated data to it (x.x.x.x should be replaced with your IP address or 0.0.0.0 to listen on all network interfaces). It is probably best to set up a static IP with your VPN provider so the server knows which port to listen in on.
Compared to stunnel and SSH tunneling, obfsproxy is not as secure. This is because it does not wrap the traffic in encryption. It is, however, somewhat easier to set up and configure, and has a much lower bandwidth overhead since it is not carrying an additional layer of encryption. This can be particularly relevant for users in places such as Syria or Ethiopia, where bandwidth is often a critical resource.
Some providers may use alternative technologies that are similar to obsfproxy. BolehVPN, for example, uses XOR obfuscation for its "xCloak" servers.
Addendum
A note on the UAE
The above advanced solutions to VPN blocking will probably prevent VPN use being detected by DPI techniques (although the United Arab Emirates has been investing heavily in advanced internet surveillance systems).
It is believed, however, that UAE ISP may also maintain an extensive database of VPN server IPs. They may be easily able to determine that you are using a VPN simply by the IP you connect to (much as websites such as Netflix do).
In reality, it seems unlikely that you will be prosecuted just for using a VPN to watch Netflix in the UAE. If you piss the authorities off in some way, however, the fact that you use a VPN may give them a dangerous weapon to use against you.
We always recommend extreme caution when considering using VPN in UAE.
A note on websites that block VPN users
This form of blocking can be challenging to overcome. Choosing a lower-profile VPN provider, or one that regularly recycles its IPs, can be effective. Trial and error is the key here.
We strongly advise that you take full advantage of any free trials and money-back guarantees that are on offer. This will allow you to find out for yourself which VPN services work for the content you want to stream.
Remember that a service which works today could be blocked tomorrow. So it is a good idea to pay for a month’s subscription at a time. This is almost always more expensive than paying annually. But if the service becomes blocked (through no fault of its own), you will not be left with a year’s subscription that is useless to you!
It might also be worth looking at Smart DNS solutions, instead of using a VPN. Smart DNS services can also be blocked, but this is more difficult to do and is less likely to happen. Fewer Smart DNS services are banned than VPN services.
Some VPN services, such as AirVPN, use fancy DNS routing. This allows you to connect to services such as US Netflix and iPlayer, even when you are not connected to servers in the US or UK (respectively)! This is not always 100% effective, but is nevertheless impressive.
Conclusion
The vast majority of VPN blocks are fairly easy to overcome using a little lateral thinking. Even where sophisticated and highly sensitive Deep packet inspections techniques are employed, technologies such as stunnel and obfsproxy are highly effective.
