The media is full of stories about malware infecting Android devices, painting a picture that undoubtedly serves the interests of antivirus app vendors who use scare tactics to convince people that they need their products.
But is this picture an accurate one? How vulnerable to malware are Android devices really, and how much do anti-malware apps actually help?
A growing backlash against anti-malware apps on the Android platform suggests that they are not really needed at all, but as we explore in this article, the situation is rather more complicated.
Can Android devices get malware?
Yes, absolutely. A highly publicized report from RiskIQ found 25,000 "blacklisted" apps in the Play Store during 2019 (although it should be noted that this was down 76.4% from a shocking 108,000 apps in 2018).
And following a recent report, Google removed 24 malicious apps that had been installed on a staggering 382 million devices from the Play Store in 2021.
In its 2021 State of Malware Report, Malwarebytes found that the most common forms of Android malware include hidden ads, such as Android/Trojan.HiddenAds and Stalkerware. Interestingly, the most common malware found, Android/PUP.Riskware.Autoins.Fota (a variant of Adups), came pre-installed on many Android phones made in China...
So there is no doubt about it: Android malware exists and it's dangerous to Android users. For many, this simple fact alone will be plenty enough argument for using anti-malware apps, but there are some considerations first.
What do Android Antivirus apps actually do?
In 2019, AV-Comparatives tested the ability of 250 of the top Android antivirus apps and services to detect the 2,000 most common Android malware variants from the past year. The results are quite eye-opening:
- Only 23 of the 250 apps had a 100% detection rate (with an additional 14 apps having a detection rate over 99%).
- Just 80 of them detected more than 30% of the malware samples with no false positives.
- Almost 40% of apps were deemed "dubious/ineffective".
Scarily, of the 138 dubious/ineffective apps, several "have already been detected either as Trojans, dubious/fake AVs, or at least as ‘potentially unwanted applications’ (PUA) by several reputable mobile security apps".
Many of these apps failed to perform any kind of actual malware scans, instead simply comparing package names to a whitelist, and if found on that whitelist declaring them to be clean. And any app not on the whitelist gets blocked, even when installed from the Play Store, resulting in many false positives.
Some of them do not even bother to add their own packages to their whitelists, causing them to report their own app.
That said, all the big-name antivirus apps that you’ve probably heard of (with the notable exception of Comodo) detected 99% or more of the malware samples, meaning that if you choose an antivirus app from a reputable anti-malware company, then it will provide real and meaningful protection for your device.
Reputable Android anti-malware apps manually scan each app, using both databases to detect known malware, and advanced heuristic analysis to detect new malware. They also monitor incoming and outgoing web traffic to sniff for suspicious activity. And as AV-Comparatives’ results show, when done right they can be very effective.
What even the best Android antivirus apps cannot do, however, is prevent app developers from harvesting data that has been obtained at least semi-legitimately, and using that data for dubious advertising purposes. The only thing that can rein in this kind of unethical behavior is Google.
What's the best antivirus for Android?
There are plenty of options on the market, and we recommend that you read our antivirus review to get a full picture of what's available. If you currently don't have an antivirus installed on your Android phone or tablet, you are putting yourself at immense risk.
The internet is full of threats and exploits that could lead to your device being attacked by cybercriminals. They could steal your data, log in to your accounts, and engage in fraud or identity theft.
We would recommend VIPRE Android Security for Android users. The software costs just $9.99 per year for a single device and gets even cheaper if you have multiple Android devices you want to protect. Once installed, the application will protect your smartphone or tablet from over 20,000 known Android viruses and malware.
What's more, the application has other security benefits including the ability to lock sensitive apps with a pin code to ensure that nobody can look at your app data should they pick up your phone in an unlocked state! It also provides real-time scanning in addition to scheduled scans, making it extremely effective at discovering threats.
Vipre is an extremely cheap way to get strong antivirus protection on your Android device! So, go ahead and use the link below to head over to Vipre's website to find out more!
What security features do Android phones have built-in?
Google does a fair amount to ensure apps in the Play Store are legitimate and to keep its users safe:
Apps are scanned for malware
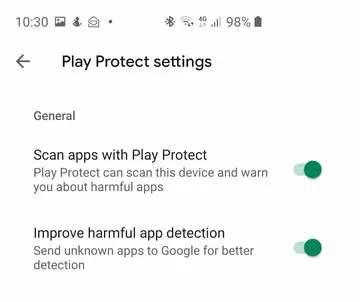
Google's Bouncer software scans all apps uploaded to the Play Store for malware, and will even remotely uninstall apps from your device if they are later discovered to contain harmful code.
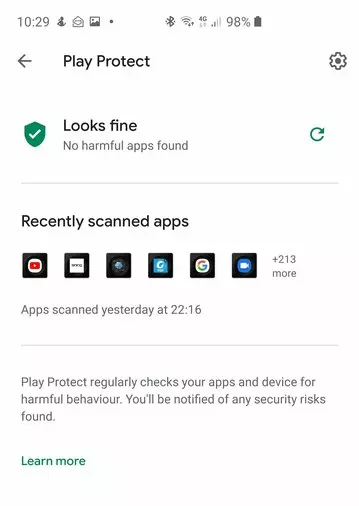
Google will even scan apps sideloaded from outside the Play Store (enabled by default in Play Protect Settings, but this can be disabled).
It should be noted, though, that it has been found that Google blocked only 68.8% of its test malware samples, making it among the worst performers in its tests.
To some extent, this is explained by Google deliberately setting its bar lower than most commercial malware apps, which make themselves look more useful by taking an aggressive approach to detection rates. But still...
Human monitoring
Google employs a human team to hand-moderate content on the Play Store. This is the biggest line of defense against apps abusing data gathered via legate-seeming permissions. Google generally does a fairly even-handed job at this, but with nearly 3 million apps in the Play Store, it is impossible to provide detailed scrutiny of them all.
Fine-grained control over app permissions
Android apps notoriously grab every permission they can, regardless of whether they are needed. Google has since brought this behavior by developers under greater control than it once was, but it still happens a lot.
You can review the permissions an app requests on the Play Store before installing it, although these are not as prominently displayed as we would like.
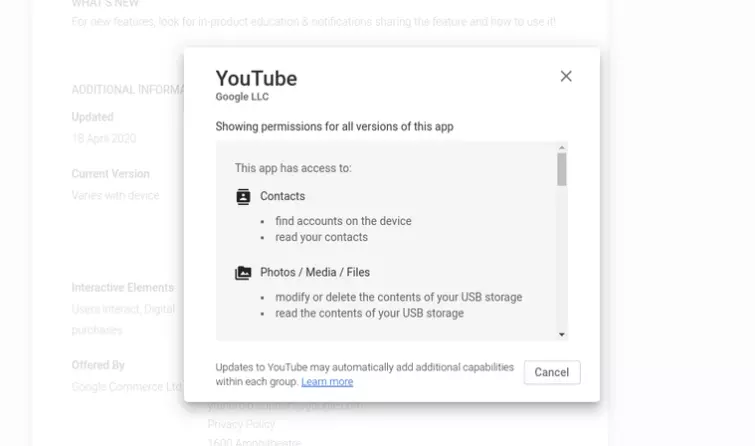
Unfortunately, you can’t opt-out of allowing certain permissions before installing the app - it's an all-or-nothing deal, although the app must ask for confirmation before accessing sensitive stuff like microphone access.
Since Android 6.0, it has been possible to gain quite fine-grained control over app permissions once an app is installed (on this writer’s Android 10 Samsung phone, go to Settings > Apps > [select app] > Permissions).
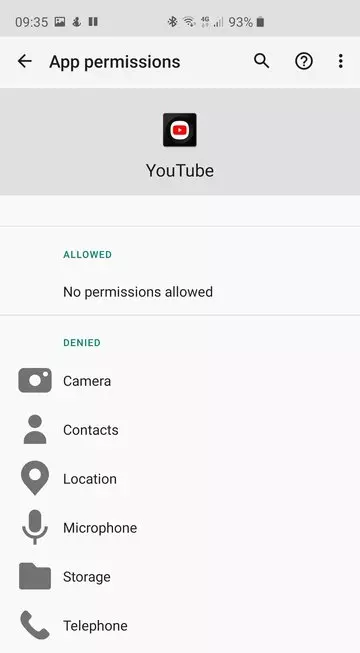
Denying certain permissions may cause apps to malfunction (or prevent them from running altogether) but at least it's possible.
We feel, however, that users should be given this level of control before an app is installed, since we're pretty sure most people don't bother to check app permissions once they've downloaded the app.
Premium-rate SMS messages are blocked
Android 4.2 fortunately put a stop to an old scam by blocking apps from sending premium-rate SMS messages. To be honest, we can think of very few apps that should have any SMS access at all.
Apps are Sandboxed
Each Android app is sandboxed, so it runs in its own environment. This should limit the damage than malware which slips through the net can do.
Is this enough?
If you only install apps from the Google Play Store, then chances are that you won’t catch any malware (although that 68.8% detection rate from AV-Comparatives does worry us a little).
To this we would add installing apps from trustworthy third-party apps stores such as Amazon and F-Droid, and even side-loading APKs obtained directly from reputable developers (such as VPN apps obtained from VPN providers’ own pages).
This is not to say that the risk is zero. VPN apps use up system resources and processing power, potentially slowing down your device and adding to battery drain. So whether you consider the risk outweighs the downsides of using an anti-malware app is very much a personal choice.
If you obtain apps from the murkier corners of the internet, however, then you probably should use a good anti-malware app from a "big name" company.
Are there any advantages to using a VPN for Android?
A VPN is not a replacement for a good Android antivirus app. That said, an increasing number of VPN apps these days offer DNS-based ad and malware blocking. In other words, they filter DNS queries, blocking connections to blacklisted domains.
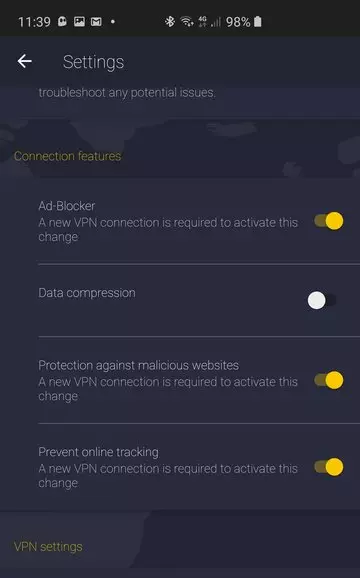
It's a simple trick that can't be relied on to protect you against tracking, unwanted ads, and installed ads contacting malicious domains. But it is often quite effective.
When using a VPN, your connection to the VPN server is encrypted, which protects you against hackers when using public Wi-Fi networks.
The widespread adoption of HTTPS by websites over the last few years has reduced the need for such protection, but VPNs still provide an extra layer of security (and will also prevent Wi-Fi hosts from selling your HTTP browsing history to advertising companies).
