Pricing
Encrypt.me makes a distinction between “passes” and subscriptions, but other than the existence of a 1-week pass, the only difference is that payment for passes does not auto-renew, while with subscriptions it does.
An unusual feature of Encrypt.me’s pricing is that in addition to personal plans, it offers family and team plans (for up to very large groups).
Encrypt.me states that you can use “multiple devices at the same time if you like” on a single unlimited data account. It seems that paying for a family or team account (presumably if the team is not too big) is largely a matter of honesty on the customers’ part.
That said, at $12.99 per month for up to five family members, the family price is quite a bargain.
Encrypt.me also offers a Mini Plan for $2.99 per month, which has a 5GB data limit. All payments are via credit/debit card only and are processed by Stripe.
New users can take advantage of a 14-day free trial, which we are pleased to note does not require any credit card details. A valid email address is required to register, and Encrypt.me takes steps to disposable ones.
Features
- Apps available for iOS, Android, macOS, and Windows
- Unlimited simultaneous connections
- Servers in 44 countries (including “Africa,” which turns out to South Africa)
- Auto-Secure
- “OverCloak”
- Content filtering
- Security audit
Torrenting is blocked by default and during the 14-day free trial, but paying customers can request that the block be lifted. Notably missing on all platforms is any kind of kill switch.
Auto-secure
When an unknown network is detected the VPN will auto-activate in order to protect your traffic.
Overcloak
When you connect to an untrusted network this feature automatically restricts access to the internet until a VPN connection is established. This feature is only available in the desktop clients.
Content filtering
This feature is not available at the time of writing but is expected to premiere soon. It uses DNS blocklists to block ads, adult content, malware, social media, and suchlike unwanted content as specified by you.
This is very similar to what most browser-based ad-blockers do, but it’s nice to have an all-in-one solution.
Security Audit
Encrypt.me underwent a security audit in 2016, with a follow-up audit published in November 2019. Unlike some other VPN services, Encrypt.me has made the full unedited text of the audit available on its website, which is something we strongly applaud. The audit covers Encrypt.me's applications, and to a limited extent, its website. Note that it is a technical security audit, and does not procedural issues such as logging. The results of the audit were positive.
No serious problems were found, and the issues which were discovered are being fixed by Encrypt.me's developers as this is being typed. This is all great but doesn't alter the fact that we detected leaks in the Window client.
Does Encrypt.me unblock Netflix?
In tests, US Netflix detected that we were using a VPN and blocked us. Connecting to a UK server did, however, allow us to watch BBC iPlayer.
Speed and Performance
Please check out our Speed Testing page for the latest weighted results, but at the time of writing Encrypt.me is number eleven on our fastest VPN list. Which is not too shoddy at all, although this is not matched by a rather ordinary max burst speed result of 198.8 Mbits/s.
DNS lookup times are fairly middle-of-the-road, although a snappy average connection time just 2.7 seconds (max 4.0s) means you won’t be left hanging around when you start the VPN.
IP Leaks
In macOS we were pleased to discover no IP leaks whatsoever. In Windows, however, we detected regular DNS leaks and also IPv6 leaks via WebRTC. At this time we cannot test to IPv6 leaks on mobile platforms, but we detected no form of IPv4 leak in Android or iOS.
Ease of Use
The website
The website looks smart enough but is rather short on hard information. And when information is available, it is often badly out of date – some articles go back to 2011! We certainly hope that things have changed during the intervening years!
A blog expends a lot of digital ink explaining why VPNs should never be considered anything close to “anonymous.” While this is true in many ways, and pointing it out is somewhat laudable for a VPN service, it also sounds to us like Encrypt.me is keen to absolve itself of its responsibilities as a VPN provider.
No, a VPN should never be regarded as 100 percent secure, and it does not guarantee anonymity. But done well, a VPN can do a great deal to protect your privacy when online. As we see in the rest of this review, Encrypt.me has simply not taken many of the steps required to do VPN privacy well (we are looking at you, connection logs and no kill-switches).
Support
The website features a number of FAQs, but these failed to answer any questions we had. Live Chat Support is available once you get past the canned responses, but the support team is mainly. based in Australia. If you contact support outside of Austalia office hours then an email response will arrive later.
As we can see in the technical security section later in this review, the answers we received were far from satisfactory.
Signing Up
Signing up for an Encrypt.me account is very easy. To take advantage of the 15-day free trial, simply provide a valid email address and password and off you go. A confirmation email provides a link to the downloads page on the website.
The Software
Apps are available for macOS, iOS, and Android. A Windows (7+) app is also available, but this is in beta only, so Encrypt.me makes no promises about its stability or security. Which as we have seen, is just as well.
There is also a “Fire OS app”, although this is just the regular Android (not Android TV) app made available through the Amazon App Store.
No setup guides or OpenVPN config files are available for manual setup on unsupported devices or with third-party VPN clients.
The macOS client
The macOS client is a fairly simple affair, but it gets the job done just fine.
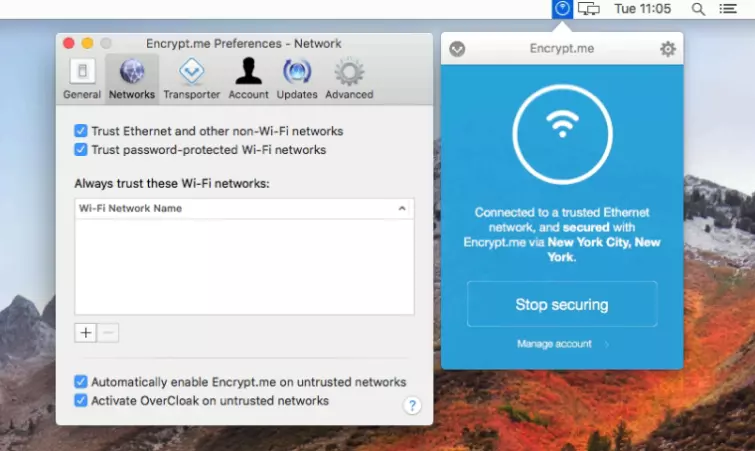
The Auto-Secure and OverCloak features are both available in macOS. The app also permits you to switch between UDP and TCP modes, which almost certainly indicates that it uses the OpenVPN protocol.
The mobile apps
Other than a Security App Lock feature in Android which secures the app with a password, the Android and iOS apps appear to be identical. The Android uses OpenVPN, however, while the iOS app uses IKEv2.
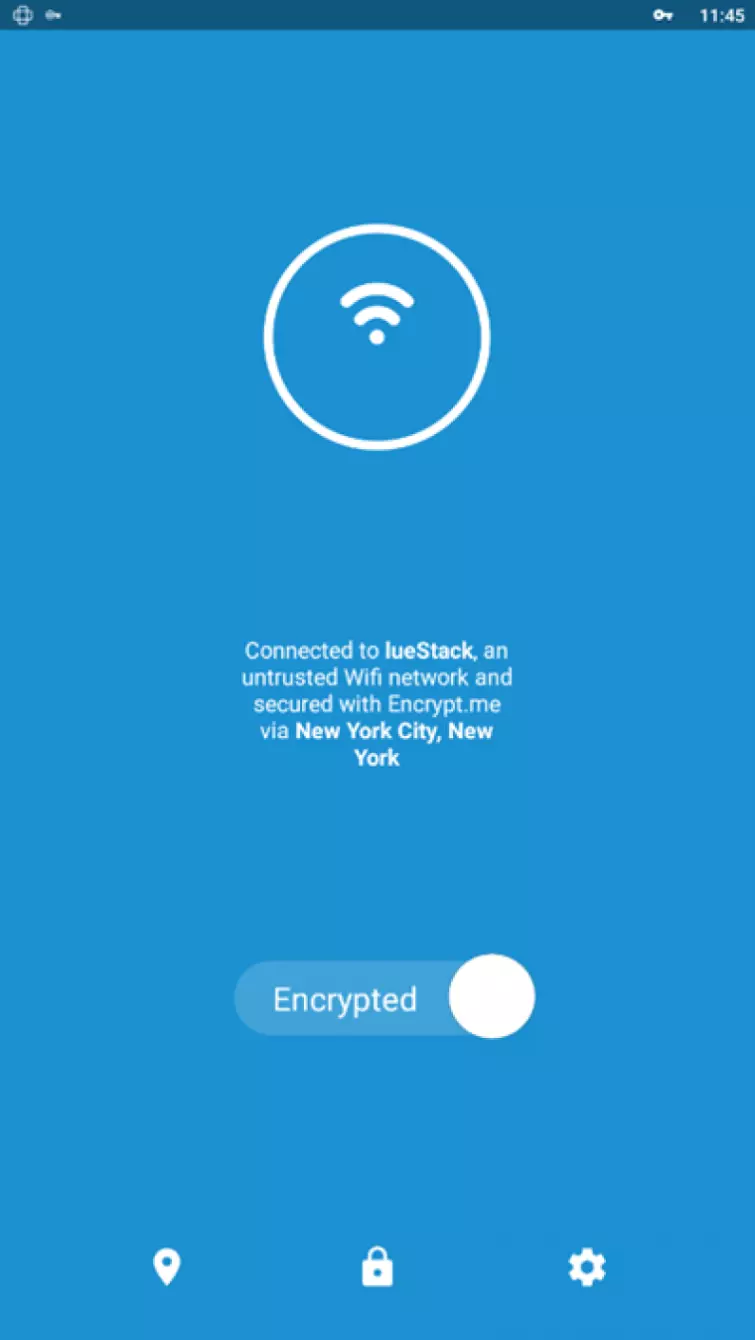
They both feature Auto-secure for WiFi networks and work generally work well. Although neither app features a switch, more recent versions of Android now have a kill switch built-in to the OS itself.
The Window client
The Windows client is very similar to the macOS client and includes support for Auto-Secure and OverCloak. It uses IKEv2 rather than OpenVPN however.
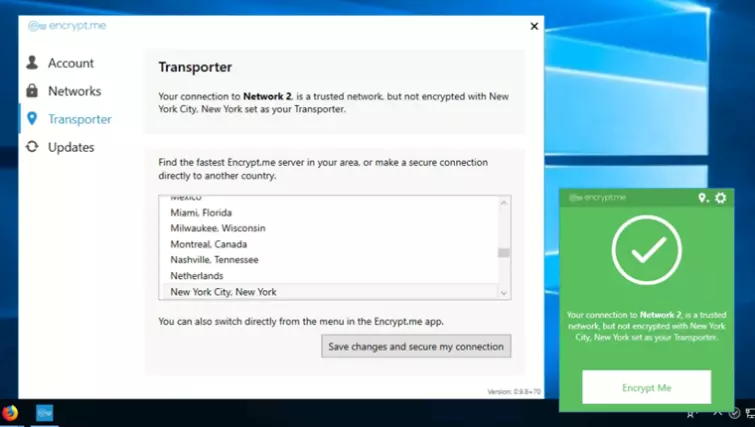
Despite what the website says, we are reliably informed the Windows client is no longer in beta. So there is little excuse for the IPv6 and WebRTC leaks we detected.
Privacy
Jurisdiction
Encrypt.me is based in Dallas, Texas, but is now owned by J2 Global, a US-based umbrella company that also officially owns seven other VPN brands. These include IPVanish and StrongVPN, and SaferVPN. In addition to these, it provides white label services for a number of other VPN products.
The United States has no mandatory data retention laws, but the scale and scope of mass surveillance by the NSA and other government agencies, as exposed by Edward Snowden, means that it is prudent to assume that all tech services which offer privacy have been compromised in some way.
Logs
Encrypt.me keeps a full set of connection (metadata) logs for users of its VPN service.
- The number of bytes sent and received
- The length of time connected
- The IP address connected from and the (virtual) IP we assign
- The source port of the outgoing connection with start and end times
This is mitigated somewhat, however, as they are only kept for 16-days before they are deleted. This is not very long but is probably enough time for a court order to be obtained if given sufficient priority.
The service also employs extensive website tracking, including the use of trackers from Google Analytics. Inside the apps analytics data is gathered by the third party Fabric.io and Google Firebase services, although it is possible to opt-out of this in-app.
Customers from or residing in the EU enjoy the usual privacy advantages laid out in the GDPR.
Technical security
The Windows and iOS apps use the IKEv2 VPN protocol, while the macOS and Android apps use OpenVPN. The OpenVPN settings used (as far as we can determine them) are:
Data channel: an AES-256-CBC cipher with SHA256 data authentication.
Control channel: full details are not available, although there was a brief mention of using AES-GCM. As this is not specified in the OpenVPN config files, we hazard that AES-256-GCM is used as both cipher and for data authentication during the TLS exchange.
We don’t know how the key exchange is secured or whether perfect forward secrecy is used.
For more information on this subject please check out our Ultimate Guide to VPN Encryption. We also asked support if Encrypt.me uses use single-occupancy bare-metal VPN servers or virtual servers (software-based VPS instances on shared servers). Or a mix…
“Complicated question. The network is huge. Mainly our own servers but we do not rent out VPS from hosting providers and build that into the network if that's what you're asking.”
Which, to be honest, leaves us none the wiser. As already noted, none of the apps feature any form of kill switch so if the VPN connection fails then your IP address will be exposed to the internet.
As also noted, and whatever the recent security audit results, we found the Windows client to be Windows rather leaky.
Final Thoughts
Other than being based in the US and keeping far more logs than we like, there is nothing very wrong with Encrypt.me except for a very leaky Windows client.
At the end of the day, Encrypt.me is a decent-enough VPN service. But in today’s highly competitive marketspace, its relatively high asking price and lack of features make its value proposition something of a hard sell.
0 User Reviews
Leave a Review
Thanks for your review!
0 Comments
Write Your Own Comment
Your comment has been sent to the queue. It will appear shortly.

There are no comments yet.