Using a VPN service is great for that warm sense of security.
This comes from knowing your online activity is private.
Unfortunately, even the most stable VPN connection will occasionally fail (disconnect from the VPN server).
When this happens, your data is no longer encrypted. Therefore your ISP will see what you get up to on the internet.
VPN dropouts can be particularly dangerous if you leave a BitTorrent client running while away from your computer. It means that every peer can see your real IP address, often for hours at a time. This is not good.
Fortunately, there are a number of things you can do to protect yourself if and when a VPN dropout occurs.
1. Use your VPN client’s kill switch
VPN Client Kill Switch
The simplest way to ensure that no programs can access the internet except over a VPN connection is to use the kill switch built into your provider’s VPN client. Choosing this setting in the client’s Settings dialogue will prevent all traffic in the event of a VPN fail.
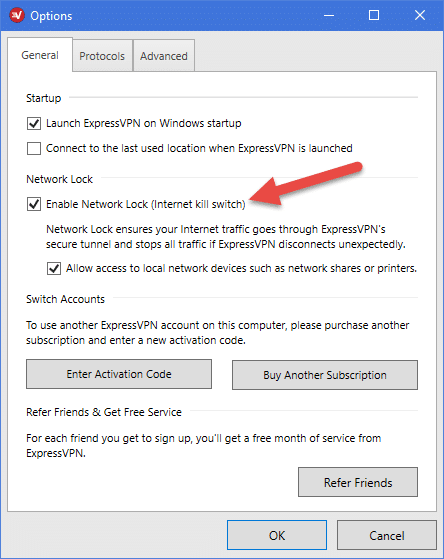
Here is the setting in ExpressVPN’s client. Kill switches may sometimes be called something else (such as "network lock”)
Almost all custom VPN clients these days feature a kill switch, although Mac clients can sometimes be less fully-featured than their Windows siblings. OpenVPN GUI doesn’t have a kill switch, but the latest beta version Tunnelblick for Mac does.
Linux Killswitch
Linux users must either configure their own kill switch using IP tables. Alternatively, they can use the custom Linux VPN clients offered by AirVPN and Mullvad.
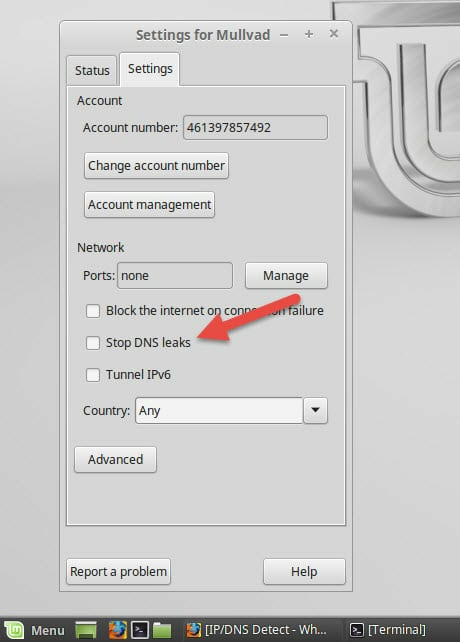
AirVPN and Mullvad are the only VPN services to offer GUI VPN clients will all the features Windows and Mac users are used to. This includes kill switches
Kill Switch on Mobile
Android apps only rarely feature a kill switch. However, all newer versions of Android (Nougat 7+) include a built-in kill switch that works with any VPN app. If you run an older version of Android then OpenVPN for Android can also be configured to work as a kill switch.
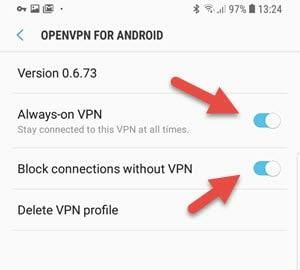
For instructions on using both these methods to setup a kill switch in Android, please see How to Install a VPN on Android.
Sad to say, but iOS users are by-and-large out of luck when it comes to kill switches.
Firewall Based Killswitch
Kill switches can be either reactive or firewall based. Reactive kill switches detect that the connection to the VPN server has dropped. They then shut down your internet connection to prevent leaks. There is a danger, however, that an IP leak could occur during the micro-seconds it takes to detect the VPN dropout and to shut down your internet connection.
Firewall-based kill switches solve this problem by simply routing all internet connections through the VPN interface. If the VPN is not running then no traffic can enter or leave your device. Firewall-based kill-switches are therefore better than reactive ones, and also serve to prevent DNS leaks.
Now... firewall based kill switches themselves come in two types. The first kind is implemented in the client, and will therefore not work if the client crashes.
The second kind modifies the Windows, OSX or Linux firewall rules. Therefore, even if the VPN software crashes, traffic will not be able to enter or exit your device. The only problem with method this is that it could, cause conflicts if you use a third-party firewall.
At the end of the day, though, any kill switch is better than none!
2. Build your own kill switch using firewall rules
The best killswitches use firewall rules to protect your connection. Thereby preventing any traffic entering or leaving your device outside the VPN interface. Although not a task for the technically faint-of-heart, it is not hard to build your own kill switch using the firewall software of your choice.
The exact details of how to do this vary by OS and firewall program, but the basic principles are:
- Add a rule that blocks all outgoing and incoming traffic on your Local Ethernet Device.
- Create an exception for your favorite DNS Server (to resolve the hostname of your VPN provider)
- Set an exception for your VPN provider’s IP addresses
- Add a Rule for your TUN/TAP or any other VPN Device to allow all outgoing Traffic for the VPN Tunnel.
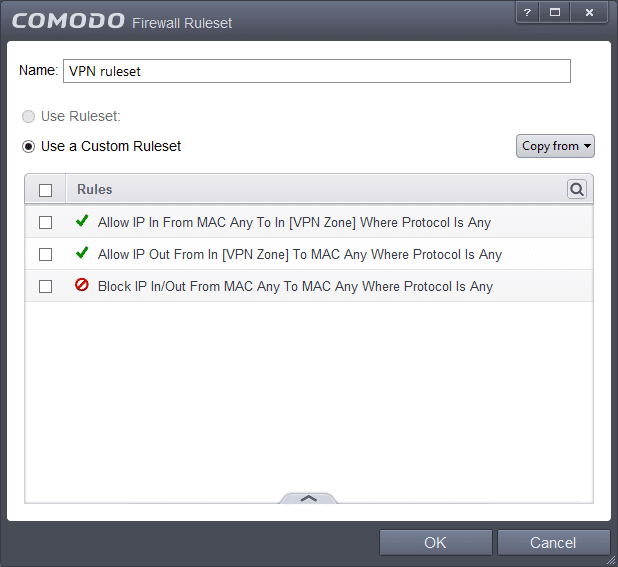
We have a detailed guide for doing this using Comodo Firewall for Windows (screenshot above). Just replace the TorGuard .exe with that of your VPN app.
Mac users can setup Little Snitch to act as a kill switch, while Linux users can configure IPtables.
DD-WRT IPtables
If you have a DD-WRT router, the following IPtables command should force all connections through an OpenVPN interface. Go to your DD-WRT control panel -> Administration -> Commands -> Firewall -> and paste in the following script:
iptables -I FORWARD -i br0 -o eth1 -j DROP
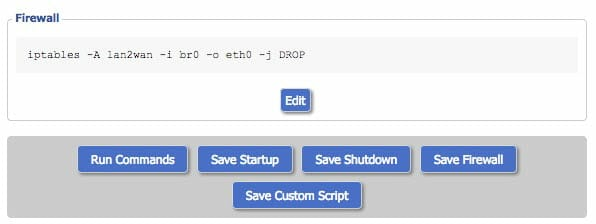
Click Save Firewall and reboot your router.
Similarly, in on a Tomato router go to Administration -> Scripts -> Firewall -> and paste in the following script:
iptables -I FORWARD -i br0 -o vlan2 -j DROP
Click Save and reboot your router.
A very big side-bonus of using a firewall-based kill switch is that it should also prevent DNS leaks. Not all firewalls handle IPv6 well, though, so it’s probably a good idea to disable IPv6 in your OS, just in case. For more information on DNS leaks, please see A Complete Guide to IP Leaks.
3. Bind your BitTorrent client to the VPN interface
As we have already mentioned, torrenters are particularly vulnerable to VPN dropouts. If you are just surfing the web, then you will probably see a notification when your VPN connection fails. You can stop then just what you are doing to manually re-enable it. Your IP address is only exposed to websites when you first visit or refresh a webpage.
Torrenters, however, often download stuff while away from their devices for lengthy periods of time. If a VPN connection fails during this time, then their IP will be exposed for all the world to see until they get back. And torrenters often have more to hide than most…
If all you are worried about is securing your torrenting activities, then some BitTorrent clients allow you to bind the client to the VPN interface.
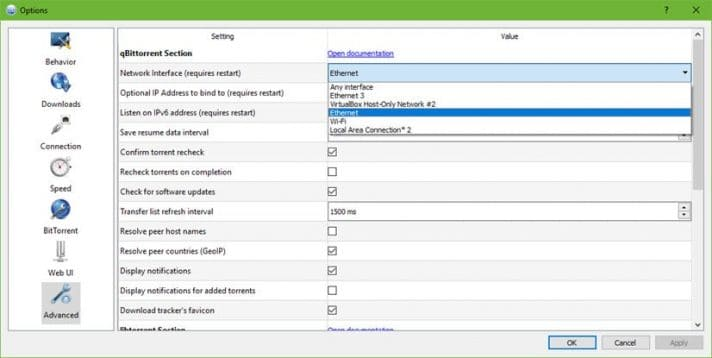
This forces the client to route all torrent connections through the VPN interface. If the VPN isn’t running then no leeching or seeding is possible. There is no data transfer to see so your IP address is not visible to other torrenters.
Just remember that this method only protects your torrent client. If your VPN goes down, your IP will be visible when using other programs such as your browser.
Please see qBitTorrent Review and 5 Best Vuze VPN Services for full instructions on how to bind those clients to your VPN interface.
For more about using a VPN when torrenting, take a look at our best VPN for torrent sites article.
Conclusion
Most custom VPN clients now include a kill switch. Therefore, turning it on to protect yourself against VPN dropouts is something of a no-brainer.
Linux users, however, are somewhat more limited with their options. The OpenVPN GUI has yet to introduce a kill switch feature (which puts macOS Tunnelblick users at an advantage).
The best option in these cases, is to make your own kill switch using firewall rules. If you find this too daunting/too much hassle, then binding your torrent client to the VPN interface may suffice.
