Using Bitcoins to purchase things online anonymously is a common practice nowadays. However, while Bitcoins may well be anonymous (when used correctly), unfortunately internet users are often not. The alarm is being raised by researchers at Princeton University, who have proven that linking an anonymous Bitcoin transaction to the actual purchaser is in many cases a simple matter.
According to the researchers, the process is achieved by linking cookies on a user’s machine to the Bitcoin transaction. For people who use Bitcoins in order to make anonymous purchases, the warning is clear: discovering who was behind the curtain is easy, very easy. In fact, the Princeton researchers are surprised that nobody has published a paper showing this before.
The study was carried out by privacy researcher Dillon Reisman, along with Princeton's Arvind Narayanan, Steven Goldfeder, and Harry Kalodner. In the paper, they use a case study subject called Alice to demonstrate just how simple it is to link cookies to Bitcoin (or any other cryptocurrency) transactions.
How Alice is discovered (taken from the Princeton paper linked above)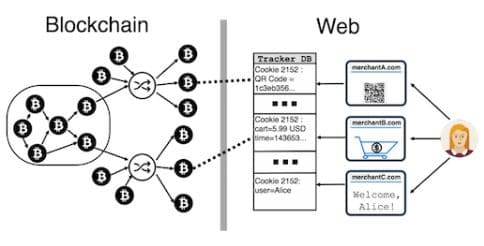
Cookie Nightmare
When we arrive at websites, cookies allow vendors to identify us and link us to past purchases. That's why, here at ProPrivacy.com, we're careful to remind people that Virtual Private Networks (VPNs) provide privacy: they do not provide anonymity. This distinction is important. While using a VPN will encrypt your data and stop your Internet Service Provider (ISP), local network administrator, and even the government from telling what you are doing online, it will not necessarily stop the website that you visit from knowing who you are.
For example, if you are logged into Twitter, Facebook, or your Google account while using a VPN, you will be able to use those services privately. However, because you are logged in, the website services themselves will know who you are.
Cookies work in a very similar way to logging in. They are little bits of data that websites leave behind in our browsers. When we return to the same URL, the cookie interacts with the website and pulls up the file associated with that particular cookie. It is an invisible process that is automatically “logging you in” to many websites that you visit.
Webmasters use cookies in order to keep tabs on the people who visit their website. This helps them to figure out statistics about how well the website is performing. It also helps them to better target you individually. Ever noticed how when you get to eBay it already knows what you want? Even before you log in? That's because of the cookies that are left in your browser.

Broken Bitcoin Anonymity
In their study, researchers at Princeton discovered that websites only need to gather small amounts of cookie data in order to discover who is making Bitcoin transactions. Even more worrying, those cookies can still identify the people behind transactions when services such as CoinJoin are used for an added layer of privacy.
CoinJoin is a service that allows people to make anonymous Bitcoin transactions. “Hang on a minute,” I hear you say, “but I thought Bitcoin transactions were anonymous!?” Sadly, this isn’t the case. Bitcoins are held together by a public ledger system called the blockchain. That public ledger holds the entire history of Bitcoin transactions and is what makes Bitcoins incorruptible.
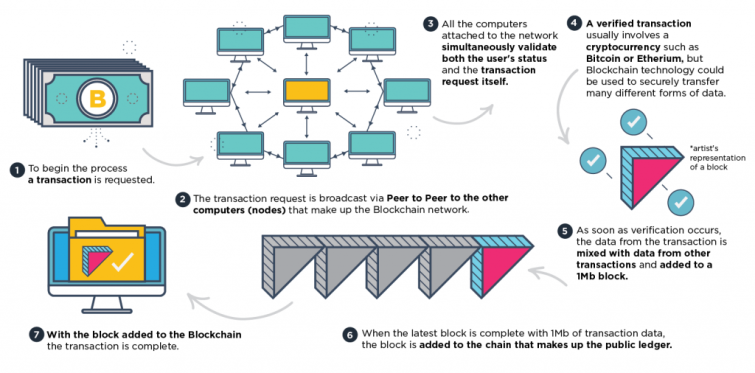
However, the immutable security provided by the blockchain also provides a way to tie people to their transactions. This is because all the transactions registered on the blockchain are completely public, which means that it is possible for anyone to see which address sent Bitcoins to which other address. When those addresses are linked to real-world identities, the transactions reveal who transacted with whom and/or for what.
Services like CoinJoin and other Bitcoin mixers (or tumblers) help people to distance themselves from their Bitcoins. They digitally launder the Bitcoins by combining many people’s Bitcoins together and mixing them up before they perform a transaction.
In the case of CoinJoin, multiple users combine several transactions into one big transaction. That one transaction sends Bitcoins from their various “input” addresses to the desired “output” addresses. Due to the fact that none of the sending addresses directly pay any of the receiving addresses, privacy is gained. Unfortunately, that process - which was perviously perceived to provide high levels of anonymity - falls short because of cookies, according to the Princeton paper.

Payment Information Leaks
Of the 130 Bitcoin-accepting vendors that were analyzed during the course of the study, the researchers discovered that 53 of them leaked payment information, to around 40 third parties. According to the researchers, it happens “most frequently from shopping cart pages.” The majority of the time, the data is being shared with third party advertisers and marketing companies.
In fact, according to the paper, “many merchant websites have far more serious (and likely unintentional) information leaks that directly reveal the exact transaction on the blockchain to dozens of trackers.”
In total, 107 of the 130 vendors were found to be leaking some kind of transaction information. Among those:
- 30 shared the transaction price in Bitcoin
- 31 allowed third party scripts to access the user’s Bitcoin address
- 104 shared the price of a transaction in dollars (or other currency)
Even when using a service like CoinJoin, the researchers found that 20 of the websites were sharing people’s names, 25 were sharing their email addresses, and nine were sharing their physical addresses.

The paper explains that there is very little that can be done to stop the process. The persistent tracking that vendors carry out is done purposefully, and there is little hope of convincing them to do otherwise. After all, vendors gain revenue from sharing consumer data with the third parties with whom they have deals.
Getting a VPN Anonymously
For people who wish to gain an extra layer of privacy by purchasing their VPN using Bitcoins, this story is important. It reveals that even when using Bitcoins, their true identity could be disclosed. At the very least, people should make the effort to clear their cookies before subscribing to the VPN (or any other purchase that they want to keep anonymous). In fact, because their IP address may be linked to the VPN at the moment of purchase, they may want to use a free VPN in order to make the VPN purchase.
For added security, people could resort to using a computer in a public library and a burner email, as well as a Bitcoin mixer service, if they truly want to keep their identity completely removed from the VPN at the moment of purchase. For more info on how to use Bitcoin mixers, please look here.
Opinions are the writer's own.
Title image credit: tiagogarciafoto/Shutterstock.com
Image credits: niroworld/Shutterstock.com, William Potter/Shutterstock.com
