Like VPN, free public proxy servers are a popular means of evading censorship and hiding a user’s true IP address. Unlike any reputable VPN service, however, the vast majority of them are dodgy as hell!
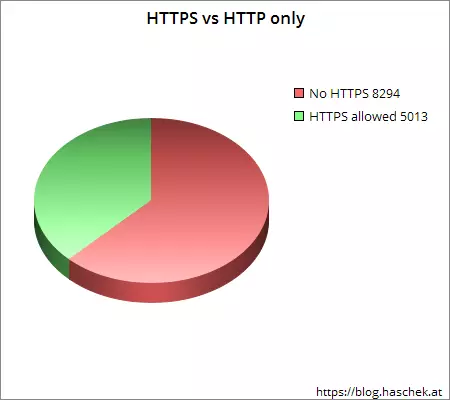
Last month, researcher published results of testing 443 public proxies using his Proxy Checker tool, which he has further updated these this week to include new results for 25443 proxy servers. He was rather shocked to find that of the 52 percent of proxies tested that were actually online, only 31.5 percent of them permitted secure HTTPS traffic!
HTTPS is used by websites to ensure that when users visit that website their connection is secured using TLS/SSL encryption. It is used by banks, online payment processors, social networks… basically every online service were it is important to secure visitors’ communications. It is the backbone of internet security.
The only reason, then, for free proxies to ban HTTPS is to snoop on the data that passes through them. As Hascek notes, this is almost certainly ‘so they can analyze your traffic and steal your logins.’
As if that wasn’t bad enough, the results show that 38.6 percent of all online proxies actively tamper with the data as it passes through them!
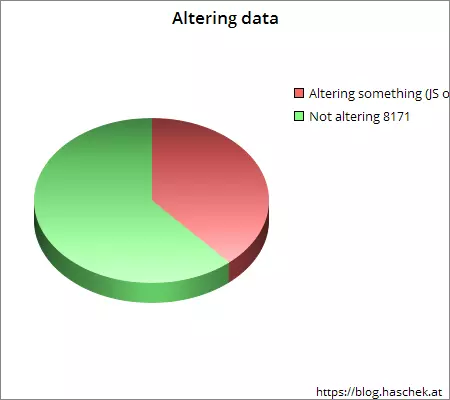
Of these, 18 percent are guilty of injecting HTML into static web pages viewed (ads), while 20.6 percent inject JavaScript. Hascek explains this use of JavaScript,
‘Most of them were to inject ads to the client. But two of them were just error messages or web filter warnings… Definitely bad adware and probably also cookie stealing… Another ad-injecting proxy was more subtle… The interesting thing here is that they point to a seemingly local JS. When the browser requests this file via proxy the proxy hijacks that request and answers with the infected JS. Very clever since it's not a cross domain JS link, like the other one.’
The simple message here is do not use public proxies! If you really feel that you must, then only use ones that permit HTTPS, and try to stick with visiting only HTTPS secured websites.
A far better option, of course, is to use a commercial VPN service. Not only do these all allow HTTPS connections, but their business model and reputations rely on protecting customers’ data. Many of the better providers go even further, taking great lengths to ensure user’ data remains as secure and private as possible. Check out our article on 5 Best Logless VPNs for an in-depth discussion about this, and the issues surrounding it.
