Pi-hole is DNS filtering software that blocks DNS requests to online advertisers and tracking companies. It is typically used to provide ad-blocker and anti-tracking protection to all devices connected to a home network.
Pi-hole will happily run on almost any Linux system, but as its name suggests, it is very resource-light and works well on low-end devices such as the Raspberry Pi (any model). Indeed, it will even work on the ultra-lightweight Raspberry Pi Zero W!
How does Pi-hole work?
The Domain Name System (DNS) is basically just an internet-wide telephone book that maps URL web addresses to the IP addresses, which computers use to identify websites. Pi-hole sits between your network and its DNS server, filtering out DNS queries for IP addresses known to belong to advertisers and analytics companies.
A Pi-hole, therefore, reduces the number of ads seen, helps prevent tracking your browsing habits for advertisement purposes, and can improve page load times since it blocks all those data-hungry apps from loading in web pages you visit.
If you have ever used an adblocker such as uBlock Origin or Adblock Plus, then you know the deal. The benefit of Pi-hole, however, is seamless protection across all devices connected to your network without the need to install any additional software.
Pricing
The Pi-hole software is 100% free and open source. It doesn’t cost a penny.
You are, however, encouraged to donate towards the project in order to cover expenses and reward the work of the volunteers who develop and maintain Pi-hole. Donations can be made via PayPal or a selection of cryptocurrencies. A number of alternative ways to support the project are also suggested.
If you are purchasing new hardware for the project, then a base Raspberry Pi costs $35 USD, to which you will also need (at minimum) to add an SD card to install the OS onto, and either a WiFi dongle or ethernet cable to provide an internet connection.
If you don't have a spare display, keyboard, and mouse, you can 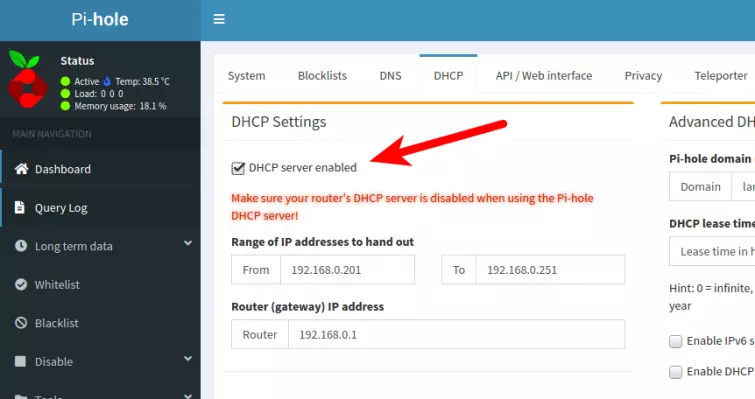
As the warning says, for this to work it is essential to disable your router's DHCP server in its Admin page. If you have a fancy router, such as one running OpenWRT, DD-WRT, or Tomato firmware, then some advanced features are available with a little extra setup.
- You can configure each device individually to use the Pi-hole as a DNS server. Check out A Complete Guide to Changing your DNS Settings for a full low-down on doing this. Just use the DNS settings you specified during setup above.
Manage your Pi-hole using the web interface
It is possible to manage your Pi-hole via the command-line. But when it comes with a gorgeous GUI web interface, why would you?
Basic statistics can be viewed by anyone connected to your LAN network, but the full statistics glory, plus admin control, are only available once you enter the correct password.
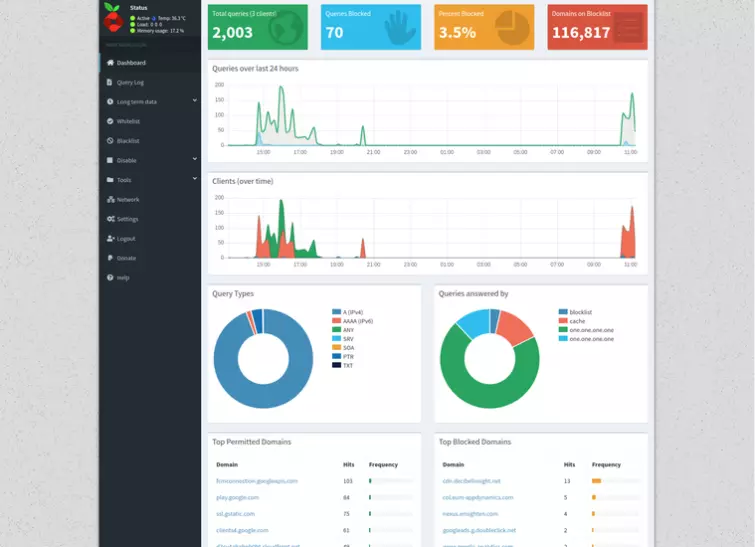
A ridiculous number of statistics are available, including how many DNS queries have been made, how many of those were blocked, which type of query they were, how they were answered, top domains that were allowed, top domains that were blocked, and more.
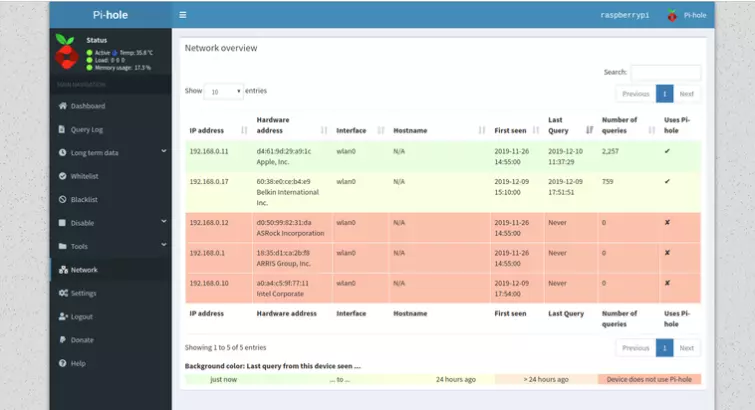
The web console provides a beautiful GUI interface for accessing a variety of logs (depending on the privacy levels you set when setting up the Pi-hole), whitelisting and blacklisting domains, monitoring your LAN network, adjusting Pi-hole settings, and more.
Final thoughts
Free and open source software that runs on $35 hardware (or less) and will provide highly effective, transparent, and fully customizable adblocker, tracker, and (limited) malware protection for all devices connected to your network? Yes, please!
As long as the idea of pasting a single command-line onto Terminal doesn't phase you, setting up a Pi-hole is very easy - just follow the prompts and go with the defaults! And once set up, the web console makes management a joy.
There is literally nothing we don’t like about this amazing software.
