What is ProtonMail?
ProtonMail is privacy-focused webmail service designed to provide the functionality and ease-of-use of services such as Gmail, but which is secure and does not spy on its users' communications in order to flog them stuff, or to hand over to the NSA... or so we thought.
It was developed by a team of research students from MIT and Harvard, headed by Harvard PhD candidate and CERN researcher Andy Yen, and was initially crowdfunded by a wildly successful IndieGoGo campaign.
Pricing and Plans
One of the most important developments is the introduction of premium plans. The very useable free tier still exists (and ProtonMail has promised it will always continue to exist), but premium plans add some very useful features, such as custom domains and web addresses, plus increased storage and messages per day.
The ProtonMail Plus plan starts at $5 per month (or $4 per month if paid yearly), but can be customized further. The ProtonMail Visionary plan starts at $30 per month, and is clearly intended for businesses.
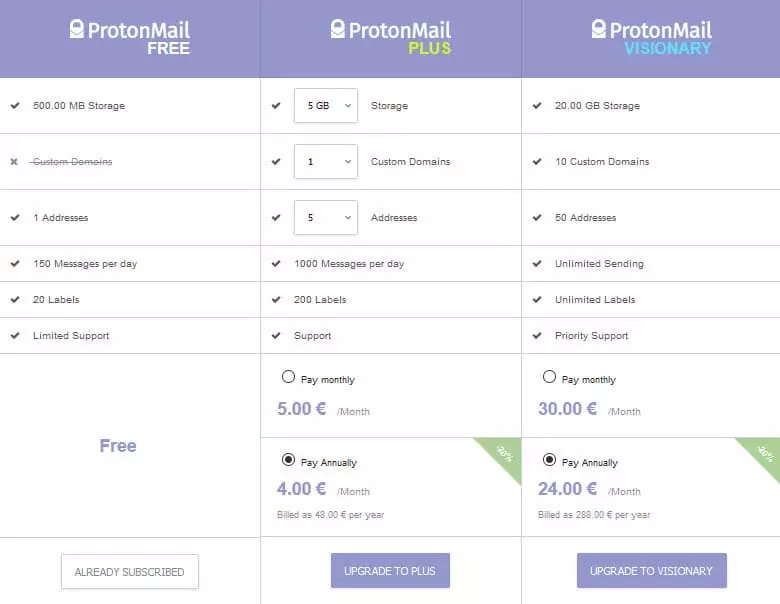
Custom Domains - if you have your own domain name, you can use this to send and receive encrypted messages using your ProtonMail account (for example at [email protected]).
ProtonMail Addresses - this is the number of @protonmail.ch or @protonmail.com addresses you can have. ProtonMail plans to add sorting features for these in a future release.
New keys are generated for each new custom domain or ProtonMail alias.
For casual users, the free service will likely be more than sufficient, but for power users, the premium extras make a welcome addition, and are an excellent way to help fund the service (remember, ProtonMail makes no money through advertising or selling your data to advertisers!).
Update: In order to help home workers during the COVID-19 lockdown, Proton VPN has increased the storage available for all paid plans:
- +5 GB for Plus plan
- +5 GB/user for Professional plan
- +10 GB for Visionary plan
All subscriptions that started before 30 April 2026 will be eligible for this increase, which is permanent as long as your subscription is active.
Features
- End-to-end encrypted emails.
- Can send encrypted emails to non-ProtonMail users.
- Self-destruct emails.
- Improved web interface with drag-and-drop messages, contacts manager, authentication logs, and more
- ProtonCalendar. This calendar encrypts event title, description, location, and participants, making it impossible for any third party (including ProtonMail) to see the details of a calendar entry.
- Apps for Android and iOS.
- Based in Switzerland (more on this later).
- Completely open source.
- Public key export (to send to other PGP users and to verify messages manually).
In response to the Covide-19 crisis, Proton is donating spare computing resources to Rosetta@home, a project run by the University of Washington that predicts the atomic-scale structure of important coronavirus proteins.
Switzerland
That ProtonMail operates out of Switzerland is a big draw for many users, as Switzerland is outside US and EU jurisdiction, and has a reputation for very strong privacy laws. Surveillance directives must be obtained through the courts and with no gagging powers targets must be notified, technical interception of electronic communications is only permitted with regards to ISP's and not “mere” Internet application providers (such as email services), etc.
Whether this reputation is entirely justified, however, is not so clear cut. It is often said, for example, that Swiss authorities have no interest in cooperating with the US and its allies, but as US tax evaders stashing their wealth in Swiss bank accounts found out in 2013, this is not always the case. Victor Vital, a trial lawyer at Barnes & Thornburg, told Wired that,
“People seem to think that data privacy laws in Europe or in foreign countries pose problems or would be a roadblock, but that's just not the case, because under those treaties the countries obligate themselves to cooperate as broadly and as much as possible.”
Even more worrying is that powerful new surveillance laws (the Nachrichtendienstgesetzt (NDG) the “BÜPF) are being pushed for by the Swiss government in the wake of last year's terrorist attacks in Paris, which will greatly expand the State's surveillance powers.
Thanks to the Swiss system of democracy, the NDG is on hold until a national referendum is held on it in June, and ProtonMail was notable for campaigning to raise the 70,000 signatures required to bring this about. The BÜPF is “up for a vote in the Parliament's spring session, but may be revised or delayed.”
I think it fair, therefore, to say that the situation is very much in the air, although ProtonMail claims it will not be affected by the NDG law, even if it is passed by the referendum.
Privacy
ProtonMail accounts are protected by two passwords, the first of which is used to authenticate the user and retrieve the correct account (and which ProtonMail keeps a copy of), and the second is kept only by the user, and is used to decrypt their mailbox. As Micah Lee, a technologist at the Intercept who focuses on privacy and cryptography notes,
“It's actually really nice that they have two sets of passwords. The login password gets sent to the server, and that's how you prove that your username is actually yours. And the second is the mailbox password, which never gets sent to ProtonMail's server. The second password runs in your browser and decrypts your messages there.”
Mail is stored encrypted on ProtonMail's servers, so the ProtonMail staff has no access to them, and these servers themselves “utilize fully encrypted hard disks with multiple password layers so data security is preserved even if our hardware is seized.”
All messages sent between ProtonMail members are encrypted. Messages to non-ProtonMail members can also be sent encrypted, or can be sent unencrypted via regular plaintext email.
According to ProtonMail, no metadata is kept and it does not log the IPs users' connect from (although there is technically nothing preventing it from doing this). As ProtonMail also points out, because messages are encrypted, there is no way for it to scan them in order to deliver targeted advertising.
Update: A major issue that I missed while initially writing this review (due to the fact that I used my existing ProtonMail account) is that ProtonMail now asks for human verification (often via SMS) while registering for a new account.
This is in many ways a quite understandable (and possibly necessary) precaution to prevent the service being abused by spammers and spambots, but it does completely undermine any notions of anonymity. Users not happy with providing an email or phone number can avoid doing so by upgrading to a premium account (which can be paid for anonymously using Bitcoins).
Finally, it is worth noting that ProtonMail has now launched its ProtonCalendar feature. This is a superb addition to the email suite, which is found in many competing email services. However, ProtonMail's calendar is unique because it actually encrypts the calendar entry's event title, description, location, and participants. This makes it impossible for any third party (including ProtonMail) to see the details of those user created entries.
Technical security
ProtonMail uses end-to-end encryption for encrypted messages, using “secure implementations” of the open source AES, RSA, and OpenPGP libraries (TLS 1.0, AES-128 CBC, DHE RSA handshake, and SHA3 hash authentication).
This is ok, although TL 1.0 is somewhat outdated, and most experts consider AES-256 to be more secure than AES-128 (this is open to debate, however, as AES-128 has a stronger key schedule).

The SSL certificates are now signed by QuoVadis Trustlink Schweiz AG,
“Advanced features of our new certificate include Extended Validation (EV), 4096-bit RSA, SHA-256 hash, and Certificate Transparency (CT). Together with QuoVadis, we will continue to stay on the cutting edge of SSL certificate technology to ensure the highest level of security for ProtonMail users.”
A big issue we had with ProtonMail was that its software was not fully open source, but this has all changed, and it is now 100 percent open source. Unlike much open source code, however, ProtonMail's has been extensively audited by a team of well-known and respected cryptographers who volunteered (for no payment) to oversee the project, looking for backdoors and other nastinesses.
So far so good, but the news is not all so rosy. As Yael Grauer from Wired explains,
“One of the big issues is that it isn't easy to know whether a message sent to another ProtonMail user is being encrypted to the recipient's correct public key, which is stored on ProtonMail's keyserver. For example, if Alice sends Bob a message encrypted to his public key, it's harder for anyone else to read the message. But since ProtonMail distributes the encryption keys to users, it has the technical ability to give Alice its own keys in addition to Bob's, thus encrypting the messages in a way that would allow it to eavesdrop.”
This is a weakness shared by Apple iMessage, but which has been solved in apps such as Signal by verifying the public encryption keys.
Another glaring problem is that all cryptography is performed within users' browsers using JavaScript. This essential in order for encryption to be performed end-to-end (rather than being performed by ProtonMail, with ProtonMail holding the private keys), but JavaScript cryptography is inherently very insecure.
This is a problem that should not affect users of the mobile apps, as long as they remember to only access their ProtonMail accounts using the mobile app, as these do not use JavaScript for their cryptography.
When sending an encrypted email to non-users, the content of the email and any attachments are encrypted. Normal email metadata information is included in the header, however, including the sender's email address, the time the email was received, and the Subject title (which can, of course, be very revealing).
The takeaway here is that ProtonMail is much more secure than “regular” webmail services, will be resistant to blanket surveillance (although it is 100 percent definite that the NSA and other security services will monitor ProtonMail accounts vigorously), and that ProtonMail will not spy on your email in order to sell your data to advertisers.
ProtonMail's claim that it provides “anonymous email” should be taken with a healthy pinch of salt, however, and it should be clearly understood that using this service is nowhere near as secure as using a standalone email client with a good PGP plugin installed (see our tutorial on using Gpg4win), or even a browser with an add-on such as Mailvelope installed.
ProtonMail in use
Signing in
Signing in requires you to enter two passwords...
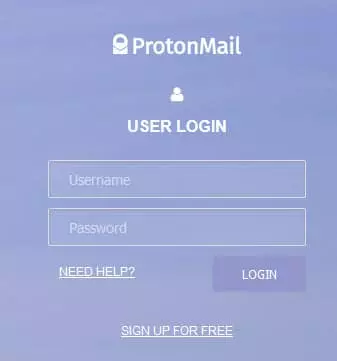
Your account password, which is known by ProtonMail...
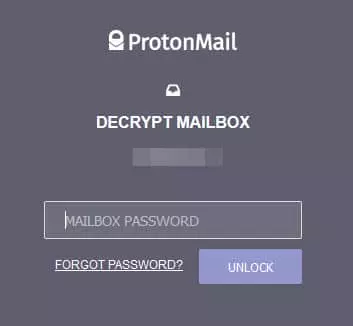
... and your mailbox password, which should be known only by yourself.
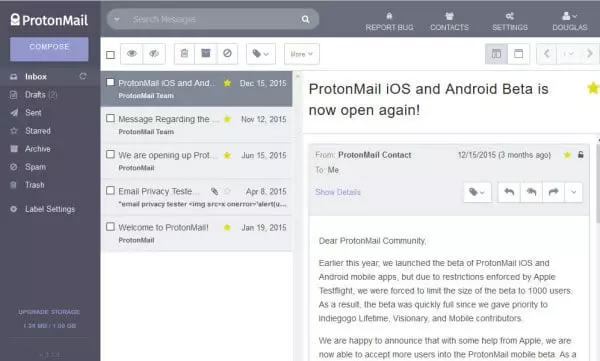
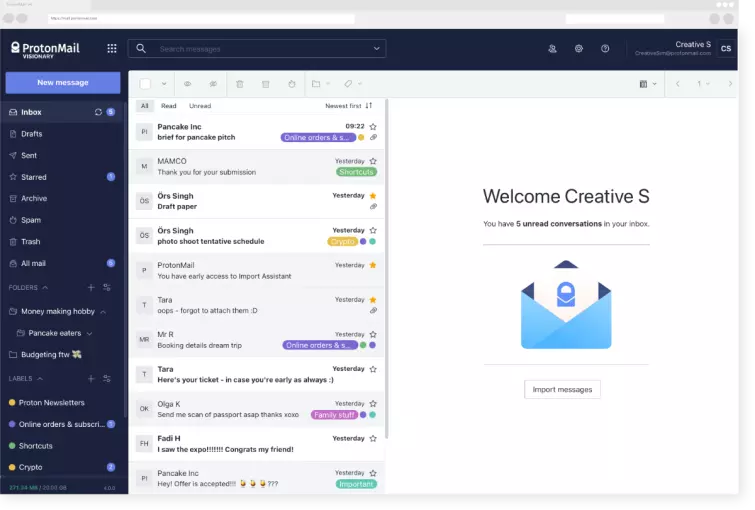
Anyone familiar with webmail services will feel instantly at home with ProtonMail. The new 2.0 interface looks good, and works smoothly.
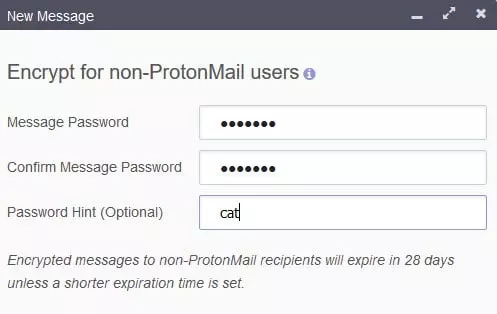
Messages sent to other ProtonMail users are automatically encrypted, while messages sent to non-ProtonMail users can optionally be encrypted. Such messages will expire (auto-destruct) in 28 days, or earlier should you choose.
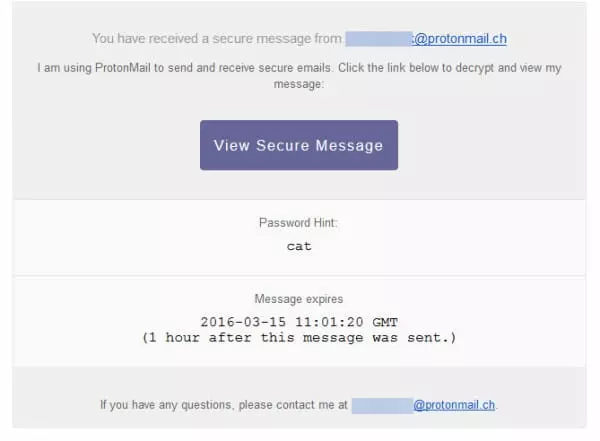
The recipient receives a link to the encrypted message (plus the hint, if used). Note that this message will expire after one hour, but also note that no metadata is hidden.

And when they enter the password...
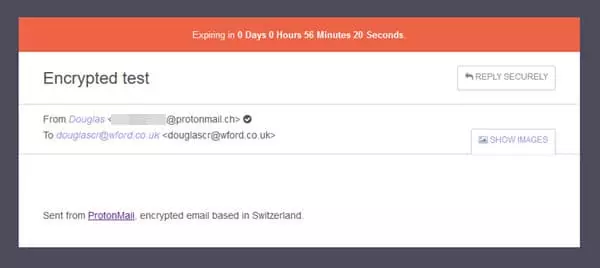
... they can read the message.

If a message has expired, then the link becomes dead.
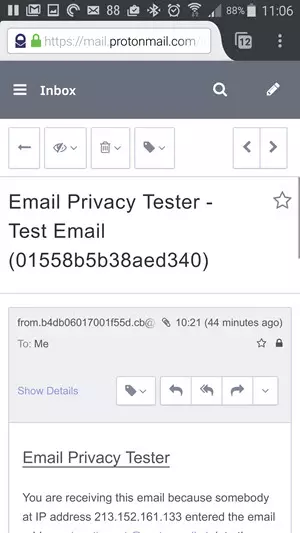
Although no mobile apps are currently available (still in Beta at the time of writing), ProtonMail's responsive website design means that it looks great in a mobile web browser.
Other Platforms
Update March 2016: The web interface is, of course, available on all platforms via your regular browser. ProtonMail has now also released apps for Android and iOS.
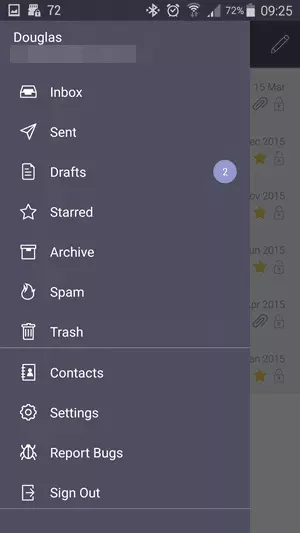
The Android app looks smart and works well
Email Privacy Tester results
I tested ProtonMail using the Email Privacy Tester tool developed by Mike Cardwell.
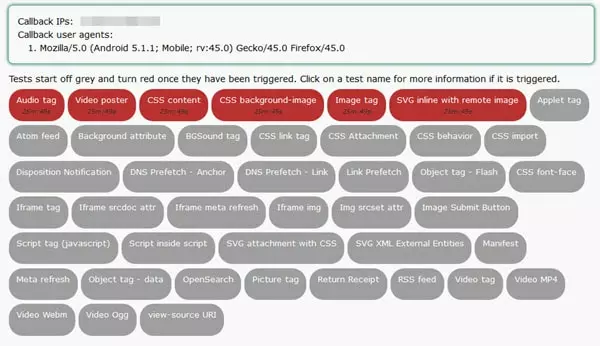
These are the same results I achieved when I tested almost a year ago and were not as good as those from Tutanota even back then
Conclusion
I Liked
- Much more secure than regular email.
- Emails are not spied on for advertising purposes.
- Easy to use and looks great.
- Completely open source.
- Can send encrypted emails to non-users.
- Self-destruct emails.
- Genuinely useful premium options (including own domains).
- Added dark mode as of ProtonMail 4.0.
I wasn't so sure about
- Nowhere near as secure as “proper” PGP email.
- Benefits of being based in Switzerland are debatable.
- Mobile apps still not available in Apple and Play Stores.
- SMS verification at registration (can be avoided by upgrading to a premium account).
I hated
- Misrepresentation of the service as “anonymous”. It's not.
- Unspectacular Email Privacy Tester results.
- Using ProtonMail will attract attention (not its fault, per se, but worth noting).
- Handing ProtonMail user information over to American Authorities.
It is often argued that when it comes to secure communication, the outdated email system is completely broken, and ProtonMail is not going to change that. Furthermore, any webmail system that implements encryption within the browser (using JavaScript) is also likely fundamentally insecure. As ProtonMail itself admits on its Threat Model page,
NOT RECOMMENDED: Edward Snowden – If you are Edward Snowden, or the next Edward Snowden, and have a life and death situation that requires privacy, we would not recommend using ProtonMail. For extremely sensitive situations, it is simply not a good idea to use email as a medium for communication.
However, ProtonMail is a very easy-to-use webmail service (on par with Gmail and suchlike) that is much more secure than most such webmail services, and which will not (cannot) spy on all your correspondence in order to target advertising (as Google, Microsoft, Apple, et al. do).
Furthermore, while it is unlikely to be secure against targeted NSA attacks (and users should be aware that the NSA will likely target users of the service), ProtonMail for most purposes (including investigations by national law enforcement bodies) provides a high level of privacy, and being based in Switzerland, it should be resilient against many legal forms of attack.
In terms of usability, ProtonMail has added a ton of features since it first started that make it very viable alternative to mainstream webmail services, and the move to fully open source is very welcome.
In short, as long as its (considerable) limitations are recognized, using ProtonMail can be a positive step towards improving your privacy and resisting blanket government surveillance. Just don't expect it to provide genuine anonymity, or to protect you if you are up to anything very illegal.
1 User Reviews
Leave a Review
Thanks for your review!
42 Comments
replied to Charlie
replied to R
replied to Lcm
replied to ET
Write Your Own Comment
Your comment has been sent to the queue. It will appear shortly.

Ryan