Surespot is an open source secure messaging app for Android and iOS. Is notable for the strong encryption it uses (56-bit AES-GCM encryption using keys created with 521 bit ECDH), support for long messages, and self-destruct messaging capability. The Android version alone has been installed 100,000 to 500,000 times. In our roundup last year of Secure alternatives to WhatsApp, we concluded that,
‘SureSpot does not support Perfect Forward Secrecy (although new keys can be generated anytime by the more paranoid), and there is a known vulnerability to MiTM attacks, but overall it is a very secure and easy to use app.’
The app achieved some unwelcome notoriety, however, when the UK’s Daily Mail
‘British jihadi brides are being groomed online using a phone app run by extreme left-wing activists, the Mail can reveal. After they are brainwashed on Twitter, Islamic State recruiters tell the young girls to communicate with them using a messaging programme called Surespot.’
This was followed in May by a Channel 4 news item,
‘ISIS militants and supporters are flocking to encrypted messaging apps, posing a challenge to security services, who say they are losing the ability to intercept data from terror suspects. An investigation by Channel 4 News can the reveal the scale of the use of one such encrypted messenger app, which functions like WhatsApp or Facebook Messenger but with very high levels of security. At least 115 ISIS-linked people appear to have used the popular app Surespot in the past six months, the investigation found.’
It is unsurprising, therefore, that the app may have attracted the interest of intelligence organizations, but it seems things might have progressed further…
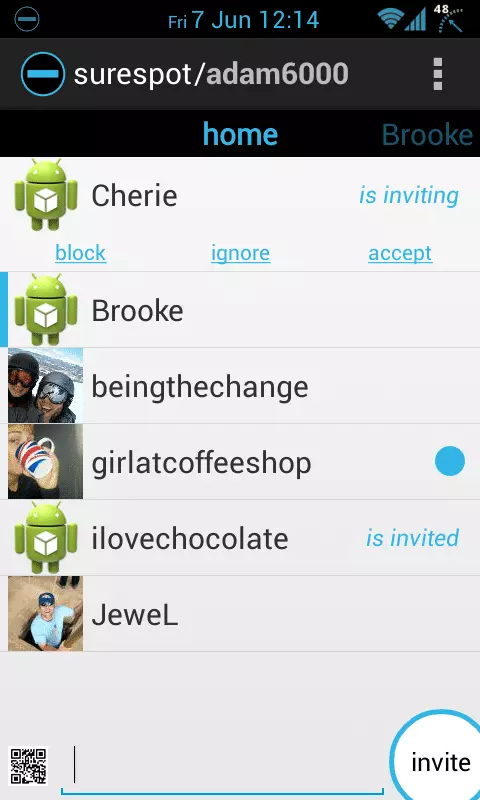
Surespot’s parent company 2fours was run by Cherie Berdovich and Adam Patacchiola (although the Daily Mail reports that Berdovich left ‘last summer.’) Unlike some security product websites, Surespot does not run a warrant canary, so George Maschke, a former Army intelligence officer and Surespot user, contacted Berdovich and Patacchiola in May last year with the flowing questions,
‘1 – Have you ever received a National Security Letter?
2 – Have you ever received a court order for information?
3 – Have you ever received any other request to cooperate with a government agency?’
He received an answer back from Berdovich saying,
‘[The a]nswer to all the questions is no.’
Maschke wrote again in November 2014 asking the same three questions, and received a reply from Patacchiola (who programmed the app),
‘1 and 2, still no, 3 we have received an email asking us how to submit a subpoena to us which we haven’t received yet.’
Clearly intrigued by this answer, Maschke emailed again the next day to ask ‘what agency or organization is seeking details on how to submit a subpoena.’ Rather worryingly, he received no reply. He also received no reply when he sent the same questions in April 2015, and when he sent the following questions in May,
- ‘Has 2fours received any governmental demand for information about any of its users?
- Has 2fours received any governmental demand to modify the surespot client software?
- Has 2fours received any governmental demand to modify the surespot server software? Has 2fours received any other governmental demand to facilitate electronic eavesdropping of any kind?
- If the answer to any of the above questions is yes, can you elaborate?’
Further attempts to contact Berdovich and Patacchiola via the Surespot app also met with no response.
In June, Chairman Michael McCaul told a Committee on Homeland Security hearing that,
‘Mobile apps like Kik and WhatsApp as well as data-destroying apps like Wickr and Surespot are allowing extremists to communicate outside of the view of law enforcement.’
Later in hearing, when asked if the FBI was pushing for encryption-defeating ‘back doors’ in software such as Surespot, FBI Assistant Director for Counterterrorism, Michael Steinbach, said ‘No,’ but,
‘I'm talking about going to the companies who then could help us get the unencrypted information. And the attribution piece – it's important to understand that, depending on the technology involved, this – and this requires, quite frankly, a technology discussion – there are tokens that are used that do not allow for attribution. So it's not quite as simple as just using other techniques or attribution. Sometimes that attribution is not there.’
Hmm… this sounds suspiciously as if, much like Ladar Levison from Lavabit, Surespot has been issued a warrant under the Patriot Act, demanding that it cooperate with authorities, while also adding a gag order to prevent the owners, on pain of jail, from alerting their users to the fact.
While Mr Levison was able to shut down his company and thereby protect his customers, this option would likely not have been available to Patacchiola (Levison was himself threatened with arrest for his actions.)
Of course, any such speculation on our part is simply that - pure speculation.
In theory, the fact that Surespot uses end-to-end encryption should make it impossible to spy on users’ communications, even if 3fours has indeed been compromised. The app’s failure to implement Perfect Forward Secrecy might provide a way to decrypt users’ messages, however, and the amount of metadata stored on the Surespot database could provide an adversary with valuable clues about users’ identities.
If we were worried about our communications being spied on, we might be tempted to look elsewhere for a secure messaging app…
