Without access to funding, US government departments are failing to renew the TLS certificates vital to the security of their websites. This is leaving visitors to many official government websites vulnerable to man-in-the-middle attacks by hackers, and preventing them from accessing key federal resources.
The alarm was first sounded by Netcraft, a UK-based internet security and research outfit who found that “With around 400,000 federal employees currently furloughed, more than 80 TLS certificates used by .gov websites have so far expired without being renewed.”
So what is a TLS Certificate?
TLS certificates are still often referred to as SSL certificates after the previous version of the technology, they are also known more generally as HTPPS certificates.
SSL/TLS certs are a key part of the HTTPS cryptographic system used to bolster every secure website on the internet, including government websites, online banking, and any online retailer where you enter your credit card details.
A TLS certificate verifies that the website your browser connects to is indeed the website you think it is connecting to. It is small data file that digitally binds a website’s public cryptographic key to an organization’s details that have been verified to own that web domain.
An HTTPS certificate is issued by a recognized Certificate Authority (CA) which certifies the ownership of a public key by the named subject of the certificate, acting in cryptographic terms as a trusted third party (TTP).
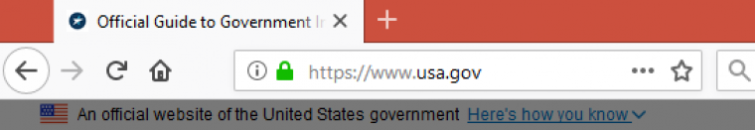
If a website shows your browser a certificate from a recognized CA, your browser will determine the site to be genuine. It will then initiate a securely encrypted HTTPS connection, and (in most cases) display a closed green padlock in the URL bar to let you know that all is well. You can then access the website as normal.
But what if all is not well?
If a TLS certificate does not match the domain visited, or if it has expired, then visitors will receive a warning message…
HSTS websites
HTTP Strict Transport Security (HSTS) is a new web security policy mechanism designed to improve security across the internet. It is impossible to connect to a properly HSTS-enabled website without a secure HTTPS connection. Which requires a valid TLS cert.
Of the 80 government sites that Netcraft discovered with expired TLS certificates, “just a handful” of them used fully and correctly (and therefore securely) implemented HSTS.
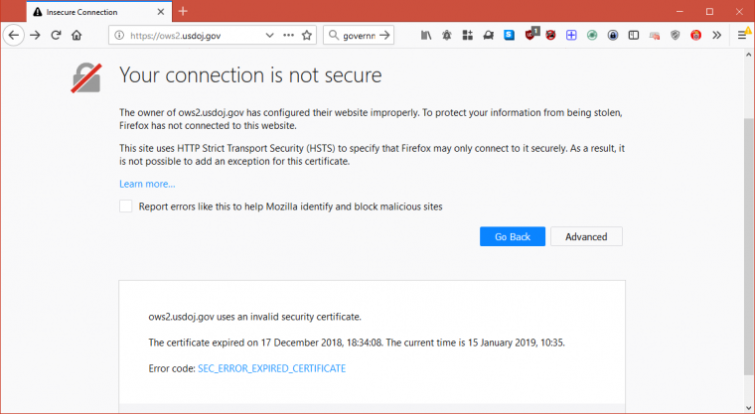
The US Department of Justice website (above) and its subdomains are protected by correctly implemented HSTS. This means visitors cannot access DoJ services at this time. Which is undoubtedly frustrating for many, but is better than the alternative when a TLS cert has expired….
Non-HSTS websites
The vast majority of websites that Netcraft discovered with lapsed TLS certificates either did not use HSTS at all or implemented it poorly, by setting the policy in their HTTPS headers but not registering the domains in Chromium's HSTS preload list.
In either case, visitors will still receive a warning, but it can be easily bypassed in order to access the website anyway. Doing so is very dangerous.
For a start, there is no way of knowing if the website they are visiting is genuine. DNS hijacking techniques can be used to redirect URL requests to fake websites, and without knowing if a TLS certificate is valid, there is often no way to tell.
Even if you are on the correct website, an invalid TLS cert means no HTTPS encryption. So everything a visitor does on the website, including all payment information they provide, is done in plain view of their internet provider (ISP) and anyone else who cares to look. Such as criminal hackers. If you see an HTTPS warning when visiting a website, do not dismiss it and proceed anyway.
Interestingly, neither of the example URLs provided by Netcraft were available at all when we visited them. It appears since the report came out developers have taken the responsible, if rather nuclear, option of addressing the issue by removing the domains from the internet entirely.
A bizarre crisis
At the time of writing the federal shutdown is on it's 25th day, and staff shortages in the White House mean that Mr. Trump is serving guests McDonald's takeaway meals.
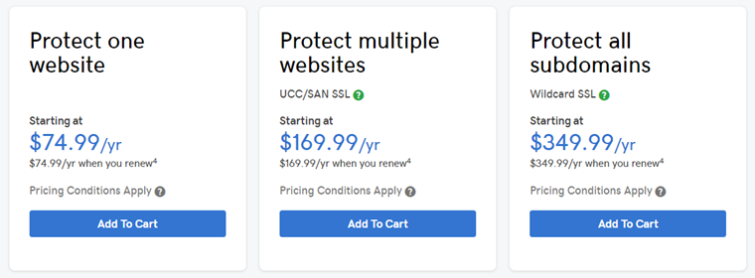
The price of a TLS certificate from GoDaddy (as used by the DoJ to secure its domains) starts at just $74.77 per year. That US government departments such as NASA and Berkeley Lab, which provide vital services to the public, simply cannot afford to renew their certificates is one of the most surreal symptoms of the ongoing crisis.
Image credit: By JPL Designs/Shutterstock.
If this story has made you reconsider your own online security, why not take a look at our best VPN services page for more information.
