Documents have been leaked online that appear to shed light on the computer game industry’s use of Artificial Intelligence (AI) to increase advertising revenue and game sales. The confidential documents appeared on Imgur two days ago, and have been doing the rounds on Twitter. The leaked documents, if genuine, reveal the terrifying lengths that the computer game industry is willing to go to in order to snoop on gamers using AI.
"Guess User Income"
The documents state that surveillance data is gathered to compile detailed profiles about users. In one example, targeted smartphones are monitored for when they reach high speeds and are traveling “on a road marked by Google maps”. When this occurs, AI uses passive listening technology to engage the smartphone's microphone. According to the documents, the AI then uses “engine noises from our engine noise hashlib to detect type of car for income guessing purposes”.
The terrifying documents also allege that phones are monitored to see if they remain in the same location for eight hours or more. If this is found to be true the target is marked as “at home”. The unconfirmed documents then go on to explain the detailed monitoring that occurs within a user’s home:
“When in home, monitor area of common walking space. Pair with information about number of staircases gathered from footfall audio patterns. Guess square footage of house.”
In a section that is marked “Schedule “Z” Location and Local Data”, it is explained how gamers are monitored during daylight hours for a possible work location, before stating:
“Cross reference average income in area. Guess user income. Guess user luxury, entertainment, and gaming budgets.”

Relaxing at Home?
A part of the document labeled “Example Highlight” then goes on to explain how it was decided that “high bonus gaming sessions during relaxing times are paradoxically not the time to encourage premium engagement.”
According to that part of the leaked documents, users are monitored using GSM data to figure out when they are “laying down" and have "the phone in their lap in their bedroom”. At that time, users are targeted with free bonuses and “non-revenue-generating gameplay ads." According to the leak, at these times “the AI severely discourages premium ads.”
Interestingly, the document claims that the AI found a specific correlation between not serving premium content in these “relaxing times” and “increased revenue in the following days.”
As if this wasn’t enough, the AI also listens, not only for keywords but also for “non word sounds." Examples include microwave sounds and even chewing noises, which are used to guess whether packaged meals have been consumed. Even a type of food is guesstimated by the AI software (chips, spaghetti, etc).
Other sounds which are deemed of interest include crying, yelling, laughing, doors slamming and many others. In fact, according to the document, there is a library of around 500,000 “non word sounds” that can be processed and cataloged.
AI also takes note of events which trigger a player to prioritize their real life over a game. These are denoted as “Distraction Events.” AI listens and attempts to guess when those distractions are over, and then attempts to trigger the user into playing again - sometimes using targeted ads on social media.
Psychological Manipulation Vs Social Engineering
A section marked “Schedule K” explains how psychological manipulation is used to coerce users into making purchases. According to that section, the industry has seen a “backlash” against psychological manipulation in favor of social engineering - which is allegedly perceived by users as developers “trying to improve the game”.
However, example K1 explains that users can be manipulated into buying the games that people on their friends list are also buying by making them think “everyone is doing it, and I just want to fit in: what is the harm?” In addition, AI may wait for players to be tired after long gaming sessions. At this point, AI can reverse the color of free and paid game titles (usually blue and red) in order to “trick a player into making a purchase by accident.”

Using Hacked Data Dumps?
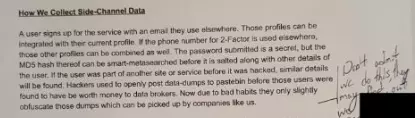
Unbelievably, it gets worse. According to the leaked documents the gaming industry also uses hacked data dumps to collect extra data about users. A section labeled “Schedule O” explains “how we collect side channel data”:
“A user signs up for the service using an email they use elsewhere. Those profiles can be integrated with their current profile. If the phone number for 2-Factor is used elsewhere, those other profiles can be combined as well. The password submitted is a secret but the MD5 hash thereof can be smart-metasearched before it is salted along with other details of the user.
“If the user was part of another site or service before it was hacked, similar details will be found. Hackers used to openly post data-dumps to pastebin before those users were found to be worth money to data brokers. Now due to bad habits they only slightly obfuscate those dumps which can be picked up by companies like us.”
It is worth noting that last section is marked with a hand-drawn arrow which has had the words “don’t admit we do this” handwritten next to it.
Protect Yourself!
For now, it remains to be seen whether this data dump is proven to be real. What we do know is that passive listening technology and AI are real, and with the right permissions apps can indeed monitor people using both GSM data and the microphone. As such, these documents appear to be damning evidence about how the gaming industry is using AI to place smartphone users under severe surveillance.
As is always the case, we urge smartphone users to be wary of the apps they install. Always check for invasive permissions before agreeing to install any app or game. If a game asks for permission to use the microphone, please remember that this type of surveillance may be occurring.
Finally, users are reminded that large hacks and data dumps happen on a regular basis. Those hacks are often leaked online, revealing people's passwords and usernames for popular online sites and services. Those passwords may also be sold to the highest bidder on the deep web. If a hacked username and password is also used on another site, hackers can easily gain entry to these other online services.
According to these leaked documents, AI software may also be using previously hacked data to gain entry to third-party services. If this is happening, then gaming companies may be breaking into secondary services to place users under surveillance and build up a detailed profile about them.
For the time being, these serious allegations have yet to be proven true. However, users are reminded to always use strong unique passwords for all of their different online accounts - to make it much harder for companies to use such practices.
Opinions are the writer's own.
Title image credit Robnroll/Shutterstock.com
Image credits: Parinya Feungchan/Shutterstock.com, Trueffelpix/Shutterstock.com, REDPIXEL.PL/Shutterstok.com
