Polish game developers CD PROJEKT RED revealed this week that they have fallen victim to a severe cyber-attack.
The company was thrust into the limelight last year after the release of the widely-downloaded Cyberpunk 2077, but it now seems they may have lost reams of private data pertaining to the game and other products.
Cyberpunk's Cyberattack
CD Projekt Red (CDPR) made the data breach public today. The stolen data is thought to contain the source code for Cyberpunk 2077 – the game at the center of the biggest digital release of all time – as well as codes for an unreleased version of another popular game, Witcher 3. Breaking news of the breach, CDPR said:
Yesterday, we discovered that we have become a victim of a targeted cyber attack due to which some of our internal systems have been compromised. An unidentified actor gained unauthorized access to our internal network, collected certain data belonging to CD Projekt capital group and left a ransom note, the content of which we released to the public.
However, although worrying, CDPR has assured customers that no actual user data has been taken, and no sensitive information pertaining to the game's players has fallen into the wrong hands. The developers have also said they have backups of all the data stolen.
The ransom note
The attack on CDPR's system was orchestrated by a hacker – or a group of hackers – looking for some sort of ransom. In an unusual move, CDPR released the actual ransom note to the public in its full entirety.
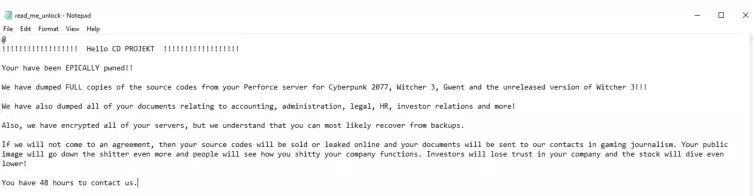
As can be seen above, the hackers inform the game developers that they have "dumped all of your documents relating to accounting, administration, legal, HR, investor relations and more" in the hopes CDPR will pay up.
As is often the case with ransomware messages, the perpetrators are keen to point out the reputational cost their actions will have on the company, perhaps hoping to inject a sense of urgency into the transaction.
The response
Despite the threats, CDPR are refusing to head to the table with the hackers, confirming that they will "not give in to the demands nor negotiate with the actor, being aware that this may eventually lead to the release of the compromised data".
Although it seems as though no ransom will be paid, this does mean the data – including the highly valuable source codes of their games – could be released to the public any time soon.
CDPR have received praise for their reaction to the problem. They asserted that they already have backups of the data and are refusing to give in to the hackers' demands, which sends a strong message to other ransomware tricksters that this method is not guaranteed to work.
The company also took the steps of making the breach public themselves, affording CDPR as much control as possible over how the issue is being framed, ensuring the PR fallout is much more manageable.
The BBC's cyber reporter Joe Tidy went even further, saying the company had "demonstrated a new gold standard response to dealing with ransomware" with the contents of just a single tweet.
A difficult few months
Unfortunately, the recent ransomware attack has been the latest in a string of problems for a developer that has faced an uphill battle since its game was released in December.
Despite being the biggest digital release ever, Cyberpunk 2077 ended up being delayed several times. When it was eventually released by CDPR, it was poorly received; many players reported that bugs and glitches were prevalent.
Several other major gaming developers have been subject to ransomware attacks in the last year. This includes some big names such as Assassin's Creed developers Ubisoft and WildWorks, the company behind Animal Jam, which has over 3.3 million active users.
What next?
The hackers were right about one thing – the attack does seem to have knocked down the value of CDPR's shares. The Financial Times charts a 7 point drop in the company's share price since trading opened this morning.
However, whether they can recover from this minor dip is an open question – presumably, the company recently responsible for the most memorable videogame release of 2020 should be able to bounce back.
A more pressing question is exactly how these hackers gained access to the information they stole – and whether that vulnerability could ever be exploited with even more sinister motivations in mind.
