Security experts at Proofpoint have released information about a recent hack that affected two Virtual Private Networks (VPNs) and eight Chrome apps in total. The VPNs involved were Betternet and TouchVPN. It's possible that their subscribers were subjected to malicious popups and data theft during the course of the suspected attack in June.
The discovery was made by Kafeine, a group of researchers at the cybersecurity firm Proofpoint in California. Those experts discovered that a relatively simple exploit involving a phishing scheme had given hackers control over a number of Chrome developers’ accounts. Here is a full list of all the apps that were affected:
- Copyfish
- Web Developer
- Chrometana 1.1.3 [source]
- Infinity New Tab 3.12.3
- Web Paint 1.2.1 [source]
- Social Fixer 20.1.1 [source]
- TouchVPN
- Betternet VPN
Simple Attack Vector
According to the researchers, the hackers used a simple phishing technique, which redirected app developers to a fake copy of the Google account login page. On this fake login page, they were fleeced of their login details, thus giving the cybercriminals access to the inner workings of the apps. From the Kafeine blog:
“At the end of July and beginning of August, several Chrome Extensions were compromised after their author’s Google Account credentials were stolen via a phishing scheme. This resulted in hijacking of traffic and exposing users to potentially malicious popups and credential theft.”
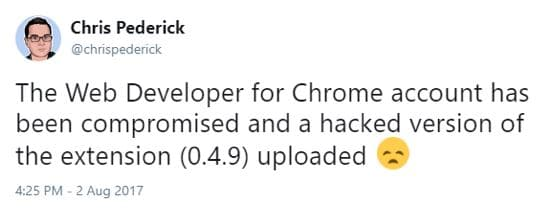
News first started to circulate about the cyberattack on 12 August, when Chris Pederick announced on Twitter that hackers had penetrated his popular extension, Web Developer for Chrome.
At that point, the Proofpoint researchers downloaded the compromised 0.4.9 version in order to isolate the nefarious code that the threat actor had injected. The researchers discovered that once the compromised Chrome extension was installed, it waited ten minutes before communicating via HTTPS with a remote Command and Control server.
From that server, the cybercriminals injected more malicious code (a file called ga.js) into the compromised Chrome extension. The domains in question were on Cloudflare, and the researchers have noted that they were taken down immediately when Proofpoint flagged them up.
In It for the Money
As is most often the case when hacking occurs, this incident involved cold hard cash. The hackers used their position within the eight compromised Chrome extensions to inject code that added unwanted Javascript. That in turn loaded adverts on top of webpages in order to create a revenue stream.

According to the researchers, most of the advert substitutions they uncovered code for were targeted at adult websites, though it is likely that adverts on other sites were also substituted.
However, many people were also served a javascript prompt informing them to “repair” their PC. Clicking on the official-looking alert redirected victims to affiliate program services from which the hackers would profit. This is what the Kafeine blog had to say about the cyberattack:
“Threat actors continue to look for new ways to drive traffic to affiliate programs and effectively surface malicious advertisements to users.
“In the cases described here, they are leveraging compromised Chrome extensions to hijack traffic and substitute advertisements on victims’ browsers.”
It is also possible that consumers suffered data loss due to the penetration.

Betternet
For users of Betternet - a VPN that is well known for serving its users with adverts - this resulted in users being served adverts by the hackers. One Betternet user going by the handle kburton07 on the website LinusTechTips, said that he had awoken on the morning of 25 June to a barrage of adverts all over Chrome:
“So, I (used to up until today) use Betternet VPN so that I could access blocked sites in college, but today when I loaded up my laptop I had adverts everywhere.
"I opened Chrome as a guest and they went. So naturally I disabled all extensions and enabled them one by one to find the problem. And to my surprise it was Betternet.
"If you look at the reviews in the Chrome Web Store everybody seems to be having the same problem so if you have it installed, uninstall it.
"I don't know whether it was intentional or whether they were hacked but until now they seem to have been reputable.”
Others Betternet users also reported having their Chrome flooded with unusual adverts, allowing Betternet to pinpoint the problem to the Chrome extension. I contacted Betternet for a comment and they confirmed that they had indeed suffered the ill-publicized hack:
“We identified and fixed this issue the same day it occurred, on June 25.”
Stay Away from VPNs that Serve Adverts
This is once again highlights the problems of using free VPNs with insecure privacy policies. VPN services are supposed to protect their users’ privacy. They do this by allowing them to conceal their location, and by encrypting their web traffic.
Free VPNs like Betternet, HotSpot Shield, TouchVPN, and many others specify in their privacy policies that they collect data from their users in order to better target adverts at them. This is highly insecure and is the opposite of what a VPN should do. The whole point of a VPN is for consumers to gain digital privacy, so using a service that expressly informs consumers in the policy that they collect and share data is counterintuitive to their purpose.

Sadly, the VPN industry is saturated with VPNs that have poor practices and care more about money than their subscribers’ privacy. It is for this reason that at ProPrivacy.com we carefully review VPNs. It's also why consumers must take great care when selecting a VPN provider.
Having said that, VPNs like Betternet do serve a purpose. For people in desperate need of bypassing censorship and who can't afford a better service, for example, these types of free VPNs can be a godsend. However, consumers need to be acutely aware of what a VPN is and isn’t doing for them. Not every VPN was created equally, and people who want solid privacy must think hard before settling for an inferior service.
Finally, it is worth noting that VPNs running as a browser extension are not considered as secure as VPNs running on custom VPN software. As such, if your VPN has a custom client, we recommend using that to connect to the VPN. This will protect you from incidents like the one in this article. In fact, browser extensions are a security nightmare in general, so you should always use as few as possible - and make sure that you only use reputable ones!
Opinions are the writer's own.
Title image credit: Evan Lorne/Shutterstock.com
Image credits: vectorfusionart/Shutterstock.com, Amirul Syaidi/Shutterstock.com
