Pricing
Gnome keyring is 100% free and open-source software. This means it is free in every sense of the word.
Features
- Systemwide password manager
- Transparent in use
- Auto-saves passwords to keyring
- Limited cross-platform syncing via Chrome passwords
- Can have multiple keyrings, each protected by its own master password
- Integrates with NetworkManager to store WEP passwords
- Create and manage PGP keys
- Create and manage SSH keys
- Passwords in open keyrings are stored in physical RAM only
- Publish and retrieve keys from key servers
A major limitation is the lack of support for passwords in Firefox. It integrates with Chrome and Chromium to store and autofill Chrome passwords but provides no integration with Firefox or the Firefox password manager.
Integration with Chrome provides limited cross-platform syncing of passwords within the Chrome browser.
Privacy and security
Jurisdiction
As FOSS software, jurisdiction is not an issue.
Technical security
Passwords (and other secrets) are stored using AES-128 encryption. This is cryptographically secure, and a stronger key schedule makes AES-128 debatably more secure than the ubiquitous AES-256.
Each keyring's master password is iteratively hashed between 100 and 2000 times using SHA-256 in order to prevent brute-forcing of the password. Once a keyring is opened, passwords and secrets are stored in physical RAM to prevent any data being accidentally, permanently stored on a disk’s swap file.
SSH connections are secured using X.509 certificates (the standard used for HTTPS connections) and/or OpenSSH encryption keys. A PKCS #11 module allows other applications to retrieve and use certificates and keys securely.
PKCS#11 is an abstraction layer that defines standards such as RSA keys, X.509 Certificates, DES/Triple DES keys, but the documentation is not clear about which standards and key lengths are used by GNOME Keychain.
The default GNOME keychain is unlocked by your OS password when you log in for transparent operation. It is possible, however, to set different passwords on each keyring for additional security. It is also possible to set a timeout period for open keyrings, after which the password must be re-entered.
The truly paranoid might want to note that the Keyring does not lock when your machine is put into suspend/hibernate mode, making it potentially vulnerable to a cold boot attack from a determined adversary who has physical access to your PC.
Support
The official GNOME Keyring and Seahorse pages provide very little useful information for casual users. Despite this, the GNOME Keyring page does provide a detailed overview of how the password manager works, plus various advanced configuration commands.
Fortunately, GNOME Keyring works completely transparently, so there is not too much to understand, anyway.
Ease of use
GNOME Keyring comes pre-installed on almost all versions of GNOME. In Ubuntu, it can be found by going to Show Applications -> Passwords and Keys. If for any reason it's not pre-installed, then it can be installed by opening Terminal and entering: sudo apt-get update
sudo apt-get install gnome-keyring
Seahorse, the GNOME Keyring GUI management app, is also usually pre-installed in GNOME. If not, then it can be installed through your GUI package manager or you can install it from the command-line in the usual way. For example, in most Debian distros with the following command:
sudo apt-get install seahorse
Initially designed for GNOME, it is possible to run GNOME Keyring on other desktop environments such as KDE or MATE.
Doing this is beyond the scope of this review, but it should also be noted that using GNOME Keyring on non-GNOME desktops means that it does not integrate with your desktop’s native apps. This limits its utility as a password manager, although it is still useful for managing PGP and SSH keys.
Using GNOME Keyring
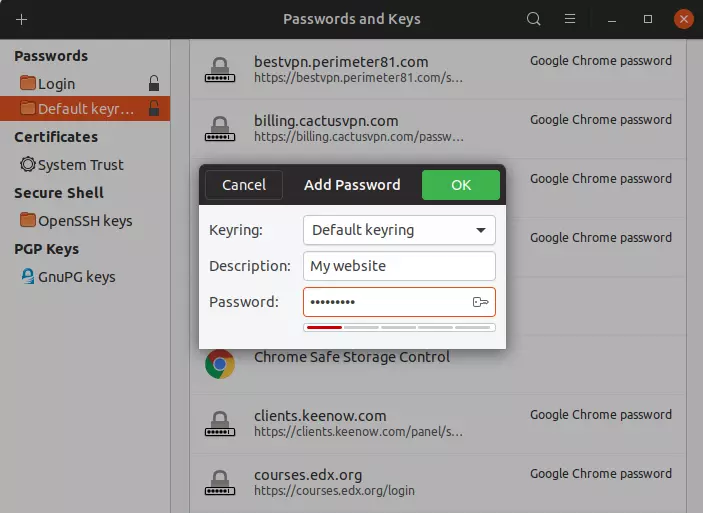
In day-to-day use, GNOME Keyring works transparently. The default keyring is automatically unlocked when you log in to your GNOME distro, and GNOME Keyring will autofill login fields in Chrome, NetworkManager and many native GNOME apps.
GNOME keyring will save new passwords to the default keyring when you enter them.
Using Seahorse
Manage passwords
Some people find it alarming that when you first open Seahorse no master password is required to access the default keyring. But remember; you unlocked the default keyring with your Linux login password when you first logged into your system.
You can lock the keyring at any time by clicking on its little padlock icon, or change the master password so it can be only opened separately with that password.
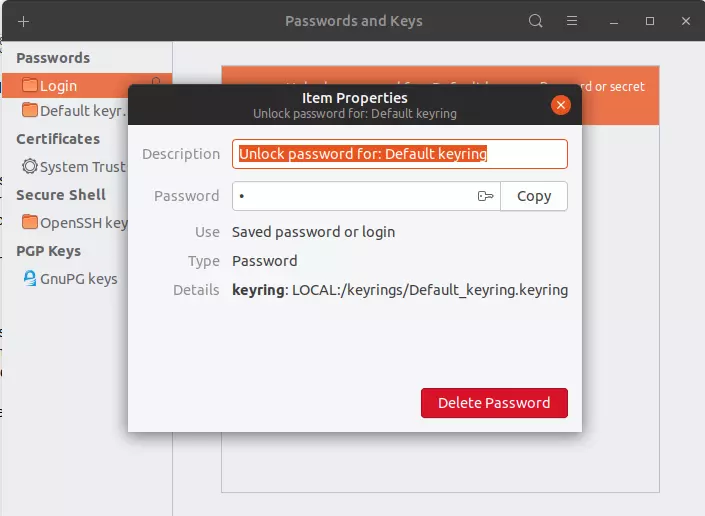
You can create as many new keyrings as you like. Once a keyring has been opened, you can click on it to explore saved passwords, delete them, and examine their properties.

You can manually add passwords to any keyring by clicking the + sign -> Password.
Manage PGP keys
Although we are focusing on GNOME Keyring/Seahorse as a password manager, in many ways its real strength lies in its PGP and SSH key management functions.
In Seahorse you can create new PGP keys pairs for encrypting and decrypting emails (for example in Mailvelope), verifying digital signatures, and more.

Seahorse allows you to sign keys (an important step, since PGP works on the principle of a web of trust) and attach ownership photos.

You can then export your public keys as .pgp files or armored .pgp files. Private keys can be exported in.asc format. Seahorse can even publish public keys to a keyserver of your choice, making it easy for other people to find them.
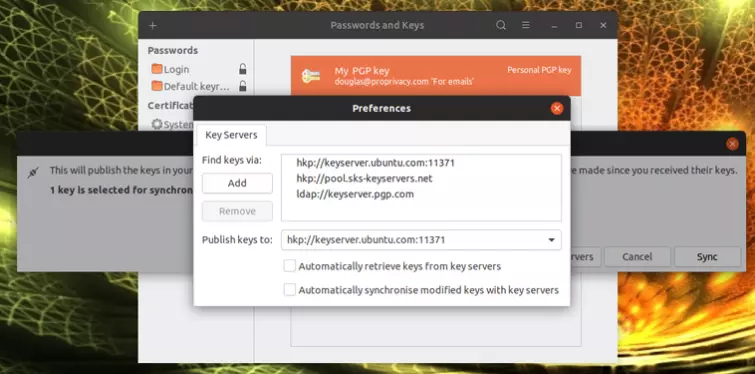
It also allows you to search for keyservers to find other PGP users’ public keys.
Manage SSH keys
Secure Shell (SSH) provides a secure way to log in to other Linux, Unix, macOS, and Windows machines remotely. Seahorse makes it easy to generate SSH keys...

... and then deploy them to log in automatically to remote servers.

Final thoughts
If you use the GNOME desktop environment, then chances are that GNOME Keyring will “just work” for you, anyway. As such, it's a handy way to auto-login to lots of stuff, although a lack of integration with Firefox is a big shame.
If you want more advanced and/or cross-platform password syncing capabilities, however, then you may also want to use something like KeePassXC or Bitwarden.
Although it is a less useful feature to many, GNOME Keyring/Seahorse really shines in its PGP and SSH key management capabilities. If you need this functionality within the GNOME environment, then you will probably come to rely on it.
0 User Reviews
Leave a Review
Thanks for your review!
0 Comments
Write Your Own Comment
Your comment has been sent to the queue. It will appear shortly.

There are no comments yet.