TeamViewer is a remote access tool developed by the German company, TeamViewer GmbH. It provides an easy and effective way to remotely control a computer to access its programs and the resources on its LAN.
TeamViewer is available for Windows, macOS, Linux, Chrome OS, iOS, Android, Windows Phone 8, and BlackBerry operating systems. And some people use it for team functions such as file transfers and desktop sharing.
Due to the global pandemic, the use of TeamViewer has increased dramatically because of people working from home in lockdown. This has left many people wondering whether the platform is actually secure.
Is TeamViewer safe?
Due to the fact that TeamViewer's primary job is to let someone else access and take over your device, it is easy to understand the concerns you might have when using it.
Could a hacker use TeamViewer to access my machine, and, if not, what is stopping them? These are reasonable questions, and it is a good idea to ask them if you care about your privacy and security.

What security does TeamViewer use?
To ensure that the data that passes over TeamViewer is safe against eavesdroppers, TeamViewer employs RSA-4096 key exchange and 256-bit AES encryption.
As a point of reference, this is similar to the encryption provided by HTTPS certificates when you connect to websites over the internet, which is secure enough to allow you to enter personal information, passwords, and payment data when using those sites. Thus, on paper, this is a highly secure form of encryption for the data that is transmitted during a session.
TeamViewer also permits users to enable two-factor authentication, which ensures that logging-in requires the code from a physical device in addition to the password.
In addition, users can force a password reset if they encounter unusual activity, and they can whitelist trusted devices to ensure that all other devices are blacklisted and cannot connect under any circumstances.
It is also worth noting that TeamViewer has some advanced security settings that the user can customize within the app. This includes things like limiting data editing privileges and recording sessions automatically for compliance purposes.
TeamViewer security concerns
Although most people trust TeamViewer for establishing remote access sessions, the platform has suffered some problems and gained bad press in the past.
In 2020, a vulnerability for the Windows version of TeamViewer (CVE-2020-13699) was discovered. This previously unknown vulnerability could allow hackers to crack user passwords leading to a compromised system.
The good news is that they found no exploits of the vulnerability in the wild before it was patched by TeamViewer, and there is no evidence that anybody ever suffered a hacked session or system because of the vulnerability.
That said, the vulnerability was considered high risk because of the potential for threat actors to exploit it remotely without any previous authentication, and users were advised to update to version 15.8.3 or higher of TeamViewer to ensure that they were not vulnerable to future attacks.
In 2017, an exploit was also reported. A Reddit user going by the name xpl0yt brought a vulnerability to light that could allow a threat actor to alter permissions, allowing them to take control of the user's mouse. On that occasion, TeamViewer also issued an update that was automatically pushed to users.
Two other vulnerabilities (CVE-2018-14333 and CVE-2010-3128) were discovered and patched in 2018 and 2010.
Of the two, the 2010 vulnerability resulted n the highest risk to users because it could allow local users, and potentially remote attackers, to execute arbitrary code and conduct DLL hijacking attacks using a Trojan.
All of the vulnerabilities have been patched in later versions of the software, and the software is much safer than it was originally for this reason. However, there is always an outside chance that more zero-day vulnerabilities could be discovered, which is why it is essential to always update your version of Team Viewer when asked to do so.
User reports
It is also worth noting that from time to time users have complained of having their machines compromised due to TeamViewer. However, it is worth noting that on those occasions, TeamViewer claims that it was the user's fault for not ensuring they use the maximum available security.
in 2016, the worst of these cases came to pass when many users claimed to have had their computer accessed and their PayPal accounts drained via TeamViewer.
According to TeamViewer, those users had failed to create strong enough passwords and had re-used passwords on TeamViewer that had been exposed on another service, thereby allowing the hackers to log in to TeamViewer.
That said, some users who were affected claimed that they had used unique passwords, creating concerns that something more serious occurred.
How to ensure greater security on TeamViewer
The best way to ensure strong security when using TeamViewer is to pick a robust password. A strong password will be 15 characters long and will contain upper and lowercase characters, numbers, and symbols.
A strong, unique password will be too hard for most people to remember, so it is a good idea to use a secure password manager to ensure the password is truly robust – and accessible to you whenever you need it.
Set up two-factor authentication, as it will ensure that a password alone is not enough to gain access to your TeamViewer account.
In addition, we recommend you follow the steps below to ensure your TeamViewer account is always secure:
- Update TeamViewer regularly to ensure you have the latest version and are patched against any vulnerabilities that have been discovered.
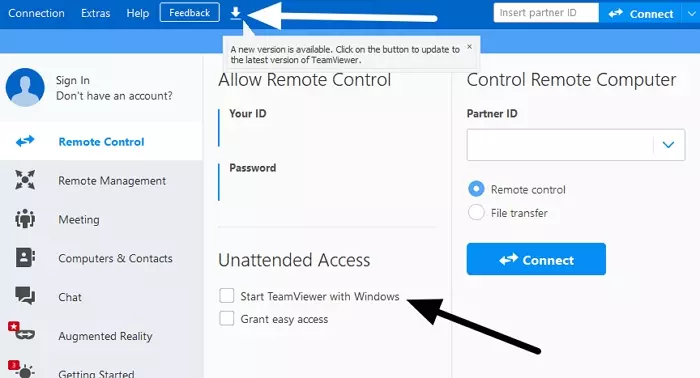
- Quit TeamViewer and shutdown the application whenever you aren't using it. By only opening TeamViewer when you need it, you will improve your security. To do so, change the setting in Remote Control so that TeamViewer doesn't launch when you start up your machine.
- Regularly check all the trusted devices. You can do this by clicking on your profile picture on the top right, followed by Edit profile > Trusted Devices, and checking any device you don't trust.
- Whitelist only devices that you trust to ensure that all other devices are blacklisted. To do so, click TeamViewer in the top left, followed by Preferences > Security > Configure (next to blacklist and whitelist). Here you can permit users to have access or deny them access with their ID. Whitelisting specific denies access to all other IDs.
- Disable easy access. This allows some devices to access your computer remotely without the need for a password. It increases the chances of being hacked, so be sure to turn it off.
What are the best alternatives to TeamViewer?
If you are interested in alternatives to TeamViewer, or would like to know how to remote access resources on a computer by using a VPN, check out the guide below for more details check out our guide on how to use your Windows desktop PC remotely.
Is it safe to use TeamViewer – Conclusion
TeamViewer has had a somewhat checkered history, with various flaws discovered over the years. This may cause concerns for some users depending on their threat model.
Despite this, it is true that TeamViewer has always been quick to patch vulnerabilities when they are found. And as long as users implement all of its security features and use a strong, unique password with two-factor authentication also enabled, there is no currently-known reason why TeamViewer should pose a security concern.
