Alternative Choices for You
![]()
From $6.67
Visit Site
Read review
![]()
From $3.69
Visit Site
Read review
![]()
From $2.19
Visit Site
Read review
Pricing
Perimeter 81 offer two core plans - the Essentials plan with a minimum of 5 users and the Premium plan with a minimum of 10 users. If you require 50 or more users, then you can negotiate a custom Enterprise plan tailored to your business’ needs.

A 20% discount is available for annual purchases. There is no free trial, as such, but there is a 30-day money-back guarantee. You can also request that staff members show you a 30-minute one-to-one demo of the product.
Essentials
*Minimum of 5 usersPremium
*Minimum of 10 usersFeatures
| Server locations | 35 |
| Simultaneous connections | 5 |
Perimeter 81 provides all the advantages of a traditional corporate VPN, including secure remote access to corporate intranet resources and protection when accessing resources over insecure public WiFi networks - all without the need for expensive physical servers and the highly qualified staff required to run them.
It also includes the following features:
- Flexible access to a wide range of less traditional network resources – such as cloud networks and IoT resources.
- It can be dynamically scaled - with on-the-fly creation of private VPN server gateways, each with its own static IP address.
- Allows administrators to assign granular access permissions - Multiple user groups with team permissions can be managed from an easy-to-use unified management portal.
- Allows administrators to monitor network activity such a bandwidth usage - keep an eye on which resources are accessed, and to detect problems and anomalies with the network.
- Provides easy-to-use apps for most major platforms - Windows, macOS, Linux (now also has Linux X64), iOS, and Android. Most of these apps include a kill switch.
- Offers users access to a large public VPN network.
- Offers automatic WiFi protection when using unknown or unsecured WiFi networks.
- Allows the use of two-factor authentication - for additional security.
- Integrates with identity providers for improved user authentication - Supported providers include Google Suite, Okta, OneLogin, and Microsoft Azure Active Directory. Perimeter 81 also has its own On-Premises Active Directory through your network’s Active Directory/LDAP Connector.
- HIPAA Compliance for Healthcare.
- Data Protection for Finance.
- Multi-Tenant Cloud.
- Single Sign-On Integration.
- Advanced DNS filtering.
- Splunk integration. Allows organizations of all sizes to search, analyze, and view the data gathered from their IT infrastructure - to have full visibility of your Perimeter 81 activity.
- 24/7 phone and live chat support.
HIPAA Compliance for Healthcare
Perimeter 81 helps healthcare companies to achieve HIPAA compliance by protecting ePHi with end-to-end encryption and built-in 2FA (two-factor authentication).
Data Protection for Finance
For Finance companies, Perimeter 81 keeps critical financial data safe against cyber threats by securing on-site and on the go access to sensitive data and organizational resources, hiding said resources from the public Internet.
Multi-Tenant Cloud
Using the handy web portal, multiple networks can be deployed, each with their own permissions. These networks can be connected to a central office, interconnected with each other or with cloud services such as AWS, Google Cloud, Azure, and other SaaS services, using IP whitelisting.
Single Sign-On Integration
Access to company resources can be managed via the web interface, providing individuals or groups with seamless Active Directory, Okta, GSuite, and Azure AD integration.
DNS Filtering
DNS filtering is a feature we see more and more in VPN clients. Usually, it's quite basic - simply blocking known ad and malware domains based on freely available blocklists (which is a tactic that can be quite effective).
Perimeter 81 has taken this a step further, however, by introducing advanced DNS filtering that gives you fine-grained control over what content is filtered. Besides simple whitelisting and blacklisting of domains, you can filter by a selection of pre-defined categories.
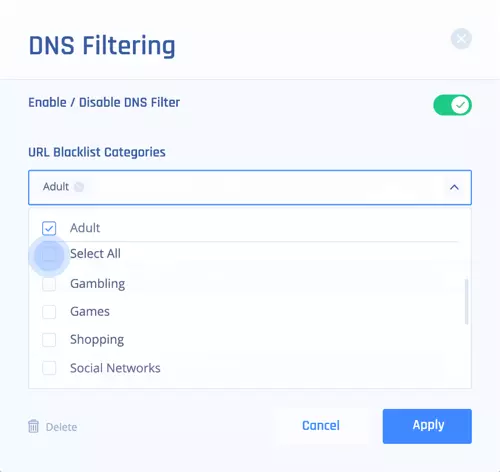
As well as blocking malicious websites and phishing domains, this type of DNS filtering is particularly useful for businesses that wish to restrict content accessed on company or personal devices (BYOD), and for preventing distractions in the workplace.
See Perimeter81's DNS Filtering feature
Performance
Speed
We only have very early speed test results at the present time. Based on these, Perimeter 81’s speeds are not terrible, but they are not very exciting, either. Raw Average / Max burst speed results are 51.1 Mbit/s / 282.5 Mbit/s, with a weighted average score of 27.01 Mbit/s.
Results have been steadily improving over the last few days, though, so may still improve markedly before leveling out. We will update this article as required.
Leak Tests
We detected no IP leaks of any kind when using the Windows and macOS apps. This includes IPv6 leaks, WebRTC leaks (both IPv4 and IPv6), and DNS leaks (both IPv4 and IPv6). We cannot test mobile devices for IPv6 issues at the time or writing but detected no leaks on an IPv4 connection.
Overall, Perimeter 81 achieves top marks. Please see A Complete Guide to IP Leaks for more information on this subject.
Ease of use
Getting Started with the Service
Perimeter 81 makes it easy for IT managers to deploy the service across their team members. Simply invite team members, who will receive an email invitation to download the Perimeter 81 client software on a wide range of platforms.
The Cloud Management Portal
At the heart of Perimeter 81 is the web portal that allows you to manage team members, servers, and permissions. It also allows you to monitor your team’s engagement with the VPN platform.
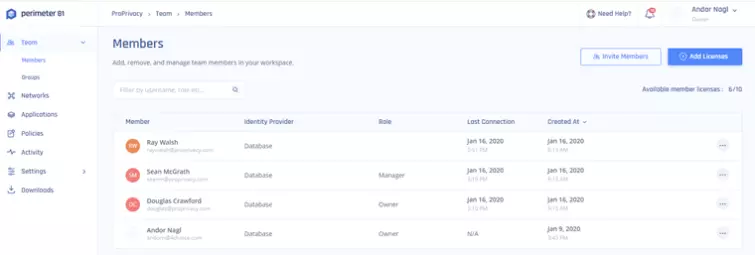
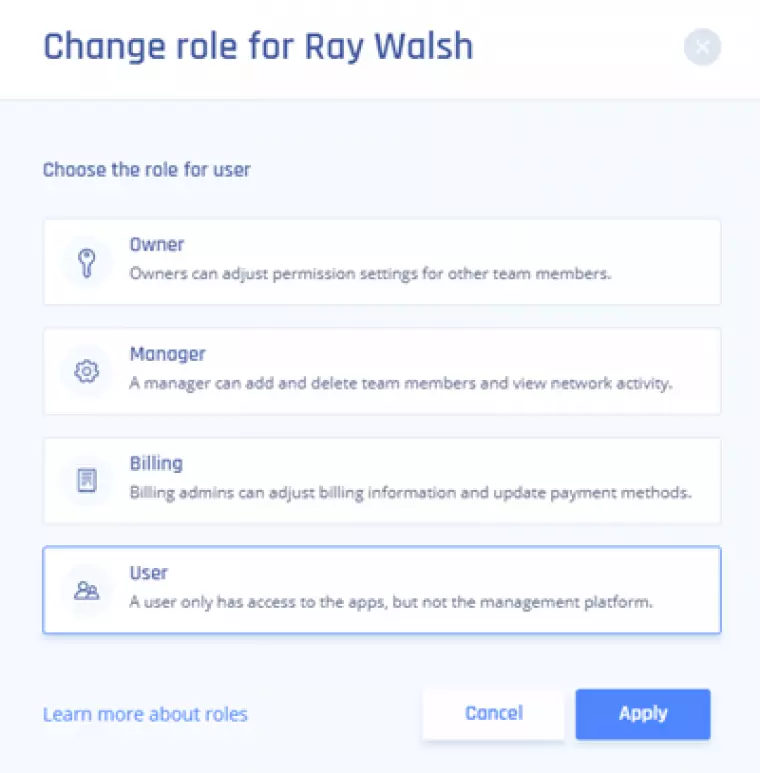
The Team tab gives you an overview of all team members. From here you can invite new members and see when team members last logged on. You can also assign them “roles” within your organization, each of which grant team members a different set of permissions.
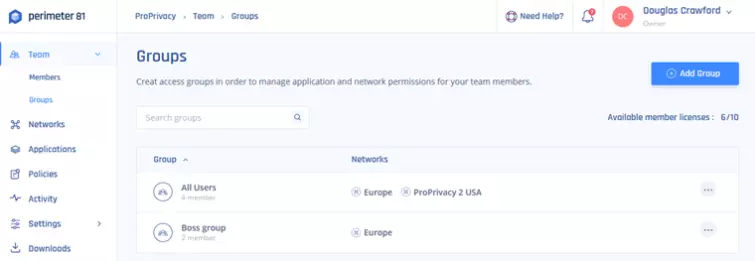
Administrators can create groups, specifying which team members can access which private servers. Since each private server can be configured to access a variety of resources, this provides administrators with a high level of customizability when choosing which team members can access which resources.
Arguably, the coolest feature of the service is the ability to create on the fly private VPN servers. These are software VPN servers run on virtual machines (VPS instances), with the VPS hosting provider largely chosen based on where its private server is located.
Creating new servers is incredibly easy.
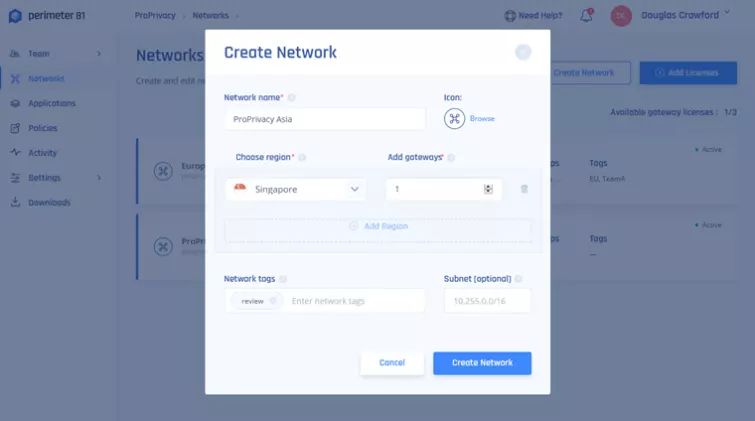
Multiple servers can be created in the same location, or in various locations around the world. It is currently possible to create private servers in various US locations, Toronto, Amsterdam, London, Frankfurt, Singapore, Bangalore, Israel, Paris, Sydney, and Tokyo.
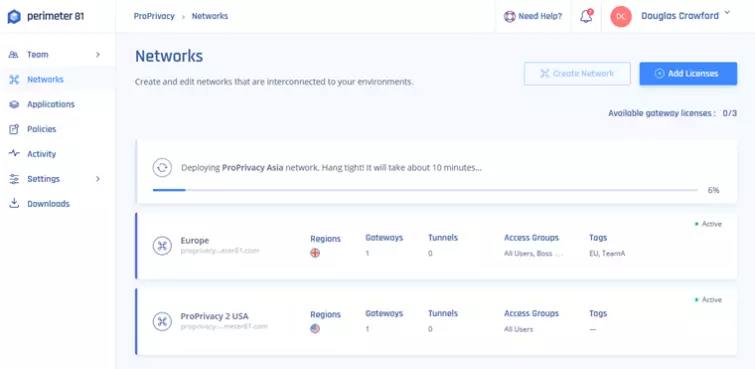
If you need another server, it only takes a minute to purchase a new license. Or, you can remove one server and create another on the same license. Once a server has been created, it takes around ten minutes to become active.
Private servers can act as secure gateways to corporate resources. Instructions are provided for connecting to LAN resources through a firewall, in addition to various private cloud resources such as Amazon Cloud Services (AWS), Google Cloud Platform (GCP), and Heroku Private Spaces.
AWS and CGP, for example, can be accessed by whitelisting incoming connections from the private server or setting up IPSec Site-to-Site VPN from those cloud services to Perimeter 81.
Mobile device integration for secure BYO setup is handled by integration with several popular third-party MDM (Mobile Device Management) services. These currently include VMWare AirWatch, MobileIron, Microsoft Intune, JAMF, and Meraki.
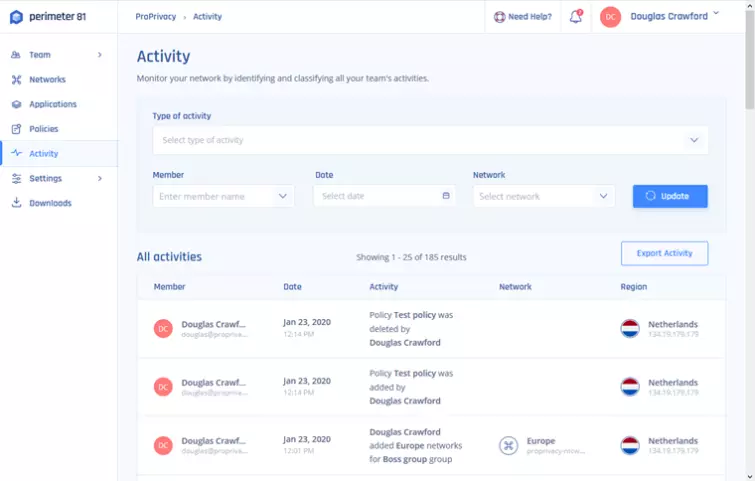
The Activity tab provides administrators with a detailed and customizable overview of their team’s engagement with the platform.
Overall, we are impressed by the Perimeter 81 cloud management platform. It provides a flexible and intuitive way to create VPN servers on the fly and then uses them to control access to a wide range of company resources.
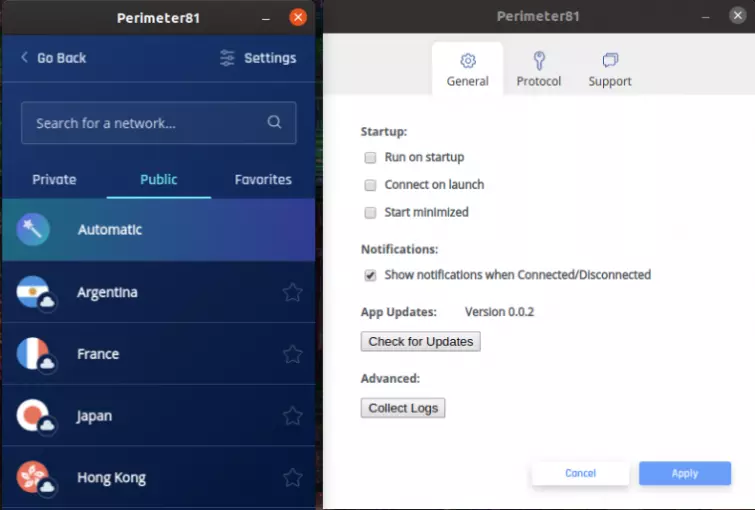
The team member apps
The team apps for Windows, macOS, and Linux (.deb) are all very similar to each other.
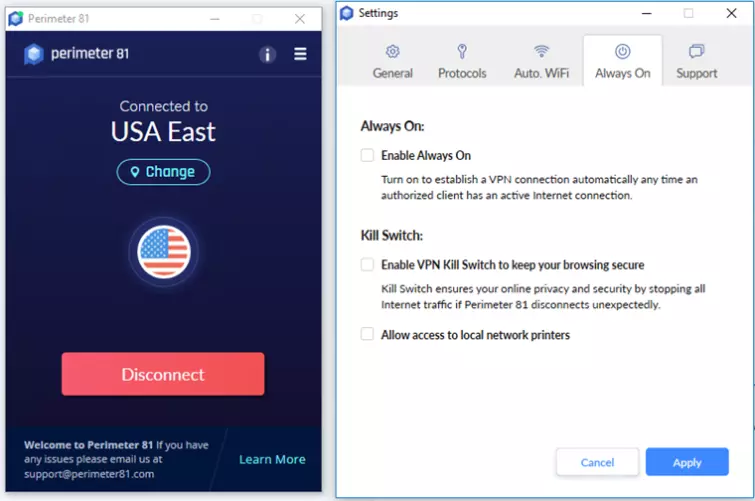
Each one supports either the OpenVPN or IKEv2 VPN protocols, while the Windows and macOS apps feature a kill switch to shut things down if the internet connection drops and “Auto WiFi,” which turns the VPN on when you connect to an unknown and potentially insecure WiFi network.
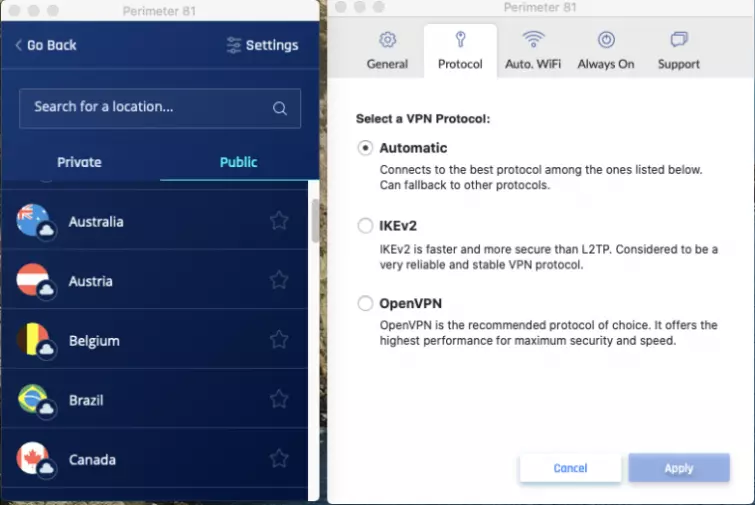
Team members can connect to your company’s private VPN servers, or to a large network public servers. In the past, Perimeter 81 used the SaferVPN network, and despite SaferVPN now being owned by a different company, not much appears to have changed in this regard (although we could be wrong about this). Whatever the situation, Perimeter 81 team members can connect to public VPN servers in 35 countries.
The mobile apps
The Android and iOS/iPadOS apps use the same UX design as their desktop cousins, and, unsurprisingly, are very similar to each other.
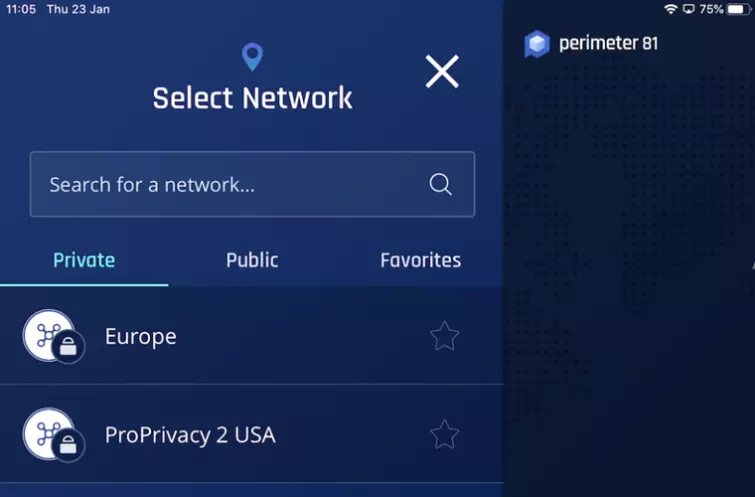
Both apps feature “Wi-Fi Security” (called Auto WiFi in the desktop apps), but the Android app has a user-selectable kill switch. The iOS app has no such option, but Perimeter 81 tells us that one is baked-in, anyway.
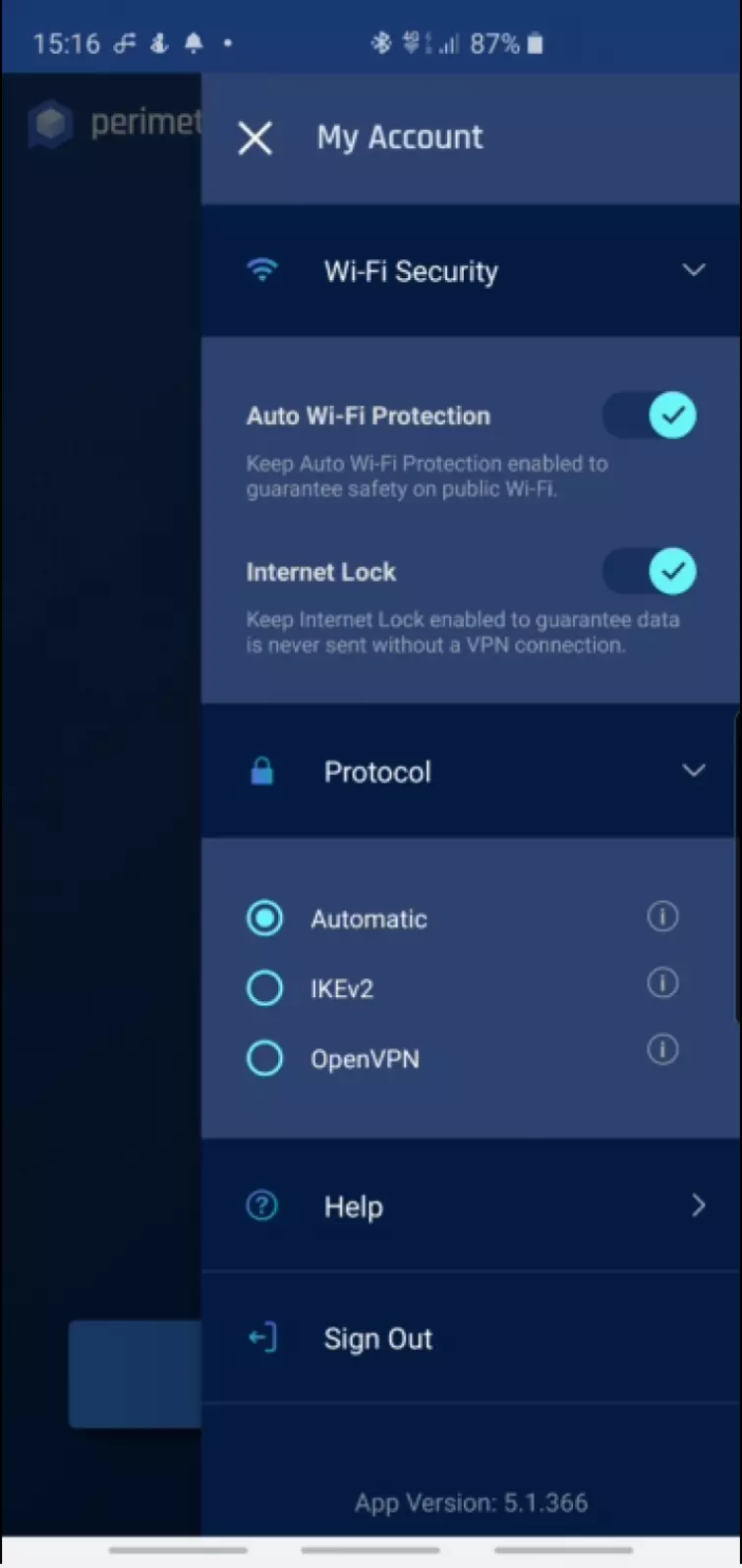
The Android also allows you to switch between OpenVPN and IKEv2, while the iOS app uses just IKEv2.
Customer Service
| Money-back guarantee | |
| 24-hour support | |
| Money-back guarantee length | 30 |
| Free trial |
There is extensive documentation on the website, including examples of how Perimeter 81 can benefit various kinds of business.
Confusingly, support can be contacted via a Live Chat client, but the response is email only. This is particularly frustrating given that Perimeter 81 describes its responses as both “instant 24/7 support” and within one day for regular Small Business customers.
In practice, with our trial account, we received email replies from anywhere within an hour to a whole day. We are pleased to say the quality of the responses was high, though.
Privacy and Security
| Obfuscation (stealth) | |
| IPv6 leak protection | |
| WebRTC leak protection | |
| Kill-switch |
Jurisdiction
Although Perimeter 81 has distanced itself from the SaferVPN brand, this VPN is based in Israel, which has strong data protection laws that strictly and specifically limit the government’s ability to spy on personal data.
On the other hand, Mossad is a close ally of the NSA, and Israel is known for the robustness of its cyberdefense operations and for its cooperation with the NSA in its mass surveillance operations.
On balance, though, we think Israel’s strong data protection laws make it a fairly privacy-friendly location.
Logs
A lot of data relating to the use of Perimeter 81 features is logged:
1. - Admin actions – We record all admin actions including inviting new team members, deleting a team member, changing team permissions, creating new cloud-based access gateways and any other action that can be taken on our management portal.
2. – Team member actions – We record connection and login timestamp, login success/error, location of the device that was connected, the hostname of the connected devices of the team members, the server the business user has been connected to and the timestamps of the connections.”
Original IP addresses are logged on private access gateways, but not on public servers.
Protocols and Encryption
| PPTP | |
| L2TP/IPSec | |
| IKEv2 | |
| OpenVPN |
Perimeter 81 uses the following OpenVPN encryption:
Data channel: AES-256 cipher with SHA256 hash authentication.
Control channel: AES-256 cipher with RSA-2048 TLS handshake encryption and SHA-256 authentication. Perfect forward secrecy (PFS) is enabled courtesy of DH-4096 Diffie-Hellman key exchange.
These settings are highly secure and meet or exceed our minimum recommendations.
Final Thoughts
Perimeter 81 is an exciting product that is well executed. Small to Medium-Sized Enterprises (SMEs), in particular, will appreciate the ability to deploy a corporate VPN network without the high costs in terms of both hardware and skilled staff traditionally associated with such a setup.
The management console allows easy and granular control over the actions and permissions of a team, and the client software works well and is easy for team members to use. The ability to create on the fly VPN servers, each with their own permissions, and then assign team members to them in a flexible way, is a revelation.
This flexibility, though, does come at a price. As is to be expected, these software VPS instances hosted on shared physical servers do not offer great speed performance.
Overall, though, we think Perimeter 81 is a groundbreaking network management and security tool that opens new possibilities for many businesses.
1 User Reviews
Leave a Review
Thanks for your review!
0 Comments
There are no comments yet.
Write Your Own Comment
Your comment has been sent to the queue. It will appear shortly.

Brian James