WPA2 is the security protocol that protects almost all modern WiFi connections. And it’s broken.
This is particularly worrying because WPA2 is the most secure WiFi security protocol currently available in general use. Unlike in the past, when older WiFi security protocols have been compromised, there is nothing to replace WPA2.
The flaw was publicly announced today following a short period of private briefings designed to give key players in the WiFi technology sector time to respond to the news.
"An attacker within range of a victim can exploit these weaknesses using key reinstallation attacks (KRACKs). Concretely, attackers can use this novel attack technique to read information that was previously assumed to be safely encrypted. This can be abused to steal sensitive information such as credit card numbers, passwords, chat messages, emails, photos, and so on… Depending on the network configuration, it is also possible to inject and manipulate data. For example, an attacker might be able to inject ransomware or other malware into websites.”
This is not good.
Your WPA2 Devices Are Vulnerable
The KRACK attack was discovered by security researcher Mathy Vanhoef of imec-DistriNet, KU Leuven. Today’s announcement builds on work Vanhoef first presented to the Blackhat hacker conference in August this year.
Vanhoef is keen to stress that almost all modern WiFi connections are affected, regardless of platform or device:
"The weaknesses are in the Wi-Fi standard itself, and not in individual products or implementations. Therefore, any correct implementation of WPA2 is likely affected. … Note that if your device supports Wi-Fi, it is most likely affected. During our initial research, we discovered ourselves that Android, Linux, Apple, Windows, OpenBSD, MediaTek, Linksys, and others, are all affected by some variant of the attacks.”
Kenn White is co-director of the Open Crypto Audit Project (OCAP):
flaw in the 4-way handshake. As I understand it, in many cases, this will be: "Throw your router away and buy a new one."
— Kenn White (@kennwhite) October 15, 2017
What Is KRACK?
The United States Computer Emergency Readiness Team (US-CERT) is a government agency responsible for analyzing and reducing cyberthreats and vulnerabilities. It has contacted around a hundred concerned organizations in order to issue a warning about the threat. It describes KRACK in the following way:
"US-CERT has become aware of several key management vulnerabilities in the 4-way handshake of the Wi-Fi Protected Access II (WPA2) security protocol. The impact of exploiting these vulnerabilities includes decryption, packet replay, TCP connection hijacking, HTTP content injection, and others. Note that as protocol-level issues, most or all correct implementations of the standard will be affected.”
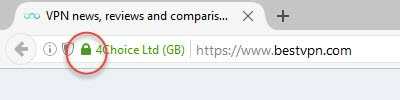
- Use a top VPN service, as a VPN protects all data traveling between your device and the VPN server. Please see VPNs for Beginners for a more detailed look at how a VPN protects your data.
- It may sound a little extreme, but if your devices aren't patched within a reasonable timeframe then you really should consider replacing them with ones that are. This is especially true of your router, as an unpatched router is a threat to the security of all WiFi attached devices.
Conclusion
KRACK is a major security flaw that affects pretty much every internet user. If you only divulge sensitive information over a secure connection, however, then you should be ok. Even better, secure all your data with the best VPN service…
Image credit:By Profit_Image/Shutterstock.com
