Apple released the iPhone X to the world on 3 November. Since then, hackers and cybersecurity researchers the world over have been racing to see if they can break the device's new facial scanning front end. At first glance, facial scanning seems to be a step up for security, but what does a Face ID really mean? And does it raise any digital privacy concerns?
Unblocked Already
Now, just a week after the release of the iPhone X, security researchers from the Vietnamese security firm Bkav claim to have fooled the facial scanner. Indeed, even before Apple released it, security experts began asking questions about whether one could crack an iPhone X with a 3D mask. Researchers in Vietnam now claim to have successfully put that method to use. According to the team, they have managed to unlock Face ID using a composite mask made of 3-D-printed plastic, silicone, makeup, and paper cutouts. According to the researchers, the mask cost them around $150 to make.
Nobody has been able to verify those findings thus far, or to prove that Bkav has really done what it claims. For this reason, we'll have to wait until a second research team manages to peer test the methodology for cracking the Facial ID system on iPhone X.
In addition, despite offering proof of concept for the method, this research shouldn’t really bother most people. That is because it is highly unlikely that anybody will have the resources, time, or ambition to make a similar mask in order to break into a device in the real world. For starters, if someone loses their phone, the hacker who finds it will need to know whose face to make a mask for, which is highly improbable.
Of course, there is the chance that in cases like San Bernardino, the authorities could create a mask to open a device. However, in that scenario, it is also highly unlikely, because the police could much more easily force a perp to look at their phone to unlock it.

Could the Police Force You to Unlock Your Phone?
The answer to this question is probably yes. Thankfully, even closing your eyes will stop the iPhone X unlocking, so this is an option. However, legally speaking DNA and fingerprints - things that make you who you are - are not protected by the Fifth Amendment. For this reason, police could gain a warrant to make US residents use their face to unlock an iPhone X.
Albert Gidari, director of privacy at Stanford University’s Center for Internet and Society, believes this needs to change. At the moment, the Fifth Amendment protects people against having to incriminate themselves. As such, people don't have to hand over their numeric passcode to the authorities.
In the case of a biometric identity method being used to protect a device, Gidari argues that the biometric identifier is being used in lieu of a code, and should be assumed to express one. However, whether this change to how the Fifth Amendment is understood will ever happen is anybody’s guess. The current system favors the authorities, so there isn’t much hope that it will change anytime soon.
Add to that, the fact that US police are once again locked out of a phone they wish they could access, and you see why it seems unlikely.
Emergency Mode
The good news is that, like with the old fingerprint scanner feature, iPhone X users can click the power button 5 times in quick succession to enter emergency mode. This turns off the facial scanner and requires the use of a passcode to unlock the device. As such, consumers do have a way to disable the facial scanner and get themselves out of the legal grey area (if they get the opportunity).
For people who have thus far been happy to use their fingerprint to open an iPhone, not much has changed in terms of the Fifth Amendment. We will have to wait to see what happens when the new facial ID is litigated on in a real case.

What we can be sure about is that at US border control (where federal agents have been known to force people to give up their passcodes), the authorities will likely be more forceful when it comes to making people open their phones. In addition, in countries outside of the US, where there are no Fourth and Fifth Amendments to protect their rights, people may find themselves more easily coerced into opening their iPhone with their face.
Trust Me with Your Face
As far as digital privacy is concerned, the facial scan itself isn’t too much of a concern. The numeric file that is created at the time that an iPhone X scans its owner’s face is only stored on the device itself. According to Apple, that file (basically a numeric code that defines the characters of someone’s face), never leaves the phone. If it did leave the phone - and go to a central database of face files on Apple servers, for example - the dangers would be massive, because (as we all know), databases can be hacked by cybercriminals.
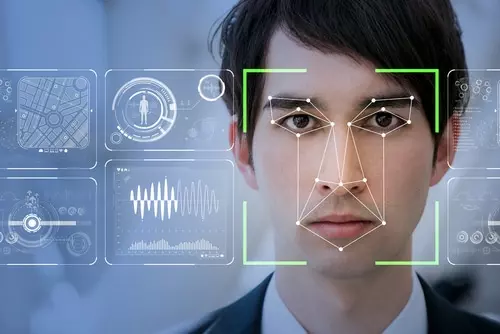
In addition, the reference file that a user’s face is compared against is encrypted and stored in a secure part of the iPhone X. Phil Schiller, Apple’s Senior Vice President for Marketing explains,
“Once a phone learns to recognize its owner, using a 3-D map made up of more than 30,000 infrared dots projected onto a person’s face, it’ll only unlock itself when it senses that the owner is looking straight at the device. The map can’t be fooled by photos or masks, and it’s stored locally in a secure part of the device. Locking the phone just requires closing your eyes or glancing away, so waving a phone in front of its sleeping owner won’t unlock it.”
The big question is: Do you trust Apple? To be fair, Apple has generally shown itself to be trustworthy. It refused to unlock one of its phones during the San Bernardino case, for example. The reality, however, is that we simply don’t know if the file is being shared with Apple and hidden away in some massive facial recognition library. If it is, that database is dangerously invasive. It is also worth a fortune. Sadly, because of the closed source nature of Apple devices, we simply do not know.
Opinions are the writer's own.
Title image credit: Artem Oleshko/Shuttestock.com
Image credits: Hadrian/Shutterstock.com
MPanchenko/Shutterstock.com
chombosan/Shutterstock.com
